In DeFi, a single smart contract flaw can lead to total capital loss. For institutions, this makes audits non-negotiable. Audits identify vulnerabilities, ensure compliance, and verify protocol security before funds are deployed. Without them, protocols face high risks of breaches, regulatory issues, and exclusion from institutional investments.
Key Takeaways:
- Why Audits Matter: Over $1.9 billion was stolen in 2021 due to DeFi vulnerabilities. Audits reduce breach risks by up to 95%.
- What Audits Cover:
- Smart Contract Review: Detects logic errors, reentrancy, and access control flaws.
- Attack Simulations: Tests resilience against flash loans, oracle manipulation, and stress scenarios.
- Regulatory Checks: Ensures adherence to KYC/AML, governance safeguards, and insurance eligibility.
- Choosing Auditors: Tier-1 firms (e.g., OpenZeppelin) and verified bug bounties are critical for credibility.
- Economic Risks: Poor tokenomics or centralized governance can destabilize even secure protocols.
For institutional investors, proper audits signal reduced risk, enhance valuations, and build confidence in deploying capital safely.
Smart Contract Audits, Security, and DeFi FULL Course | Learn smart contract auditing
sbb-itb-c5fef17
Key Components of a DeFi Protocol Audit
A proper DeFi audit is typically divided into three main areas, each addressing specific risks. These components provide a structured framework that ensures a protocol is secure and ready for institutional investment.
Smart Contract Code Review
The backbone of any audit is the code review. Auditors compare the intended business logic with the actual code to uncover logic errors – cases where the code works as written but not as intended [4][6]. This ensures that the smart contract functions as promised by the developers.
The process blends automated tools and manual inspection. Tools like Slither, MythX, and Echidna are used to scan for common vulnerabilities such as reentrancy attacks and integer overflows. However, automated tools only catch about 68% of typical bugs, leaving the remaining 32% – often complex logic flaws – for human experts to uncover [8].
Manual reviews dig deeper, identifying risks like economic exploits, broken access controls, or vulnerabilities in integrations with external oracles and bridges [1][6][8]. For highly sensitive protocols, auditors may use formal verification, employing mathematical proofs to confirm the smart contract behaves as expected under all scenarios. This approach can also confirm the absence of specific vulnerabilities like reentrancy [3][7].
Once vulnerabilities are identified, auditors verify fixes to ensure they don’t introduce new issues or alter trust boundaries. Institutional investors should ensure that all critical and high-severity issues are resolved and verified by the auditor – not just rely on an audit badge [1][3].
Dynamic security testing follows, simulating attacks to test the protocol’s resilience.
| Vulnerability Class | Description | Detection Method |
|---|---|---|
| Reentrancy | Recursive calls draining funds before state updates | Manual Review / Formal Verification [3] |
| Access Control | Unauthorized users accessing sensitive functions | Manual Review / Static Analysis [3][6] |
| Oracle Manipulation | Distorting price feeds to trigger liquidations | Threat Modeling / Economic Simulation [3][8] |
| Integer Overflow | Math operations exceeding variable limits | Automated Tools / Solidity 0.8+ [3] |
| Logic Flaws | Errors in business logic (e.g., reward miscalculations) | Manual Review / Specification Mapping [4][8] |
Security Testing and Attack Simulations
Static code reviews are just the start. Security testing evaluates how a protocol handles active threats.
Fuzz testing tools like Echidna are used to uncover unexpected edge cases and state changes that developers might not have anticipated [8]. Meanwhile, attack simulations deploy the protocol on testnets to mimic real-world threats such as flash loan attacks, price oracle manipulation, or liquidity draining during market stress. For example, auditors might simulate a $10 million flash loan or a rapid 10% price drop to test the protocol’s resilience.
Penetration testing focuses on administrative security. This includes verifying that emergency pause functions work correctly if an owner’s wallet is compromised and ensuring multisig governance and timelocks operate as intended during simulated exploits. Tools like Phalcon and Tenderly allow developers to test transactions without incurring gas fees, helping identify potential reverts or excessive permissions [8].
"Security isn’t a checkbox. It’s a habit." – Dennis Highfill [8]
Modern audits also include stress tests to confirm that defense mechanisms hold up under pressure, which is critical for protocols handling institutional capital.
Compliance and Regulatory Verification
DeFi protocols serving institutional users must meet strict regulatory requirements, including publishing audit reports [10]. Compliance verification ensures adherence to these rules, including KYC/AML standards where applicable [1].
For institutions, compliance directly impacts fundraising, partnerships, and market positioning [10]. Auditors evaluate governance structures, such as multisig wallets and timelocks, to reduce risks like "rug pulls" or unauthorized changes by developers [9]. For instance, critical protocol updates should be safeguarded by a timelock (minimum 48 hours) and a multisig wallet (e.g., 3-of-5 or 5-of-9) to prevent centralized failures [9].
Audit quality also influences insurance eligibility. DeFi insurance providers often base coverage terms and premiums on the depth and frequency of audits [1][10]. It’s worth noting that 70% of the $1.8 billion lost to smart contract exploits in 2025 stemmed from vulnerabilities that could have been identified through a structured audit [10].
Regulatory checks go hand-in-hand with technical audits, addressing operational and governance risks alongside code vulnerabilities. Auditors ensure protocols follow the principle of least privilege for roles like minters, pausers, and upgraders [10]. They also verify the use of reliable pricing mechanisms, such as decentralized oracles (e.g., Chainlink) or TWAP (Time-Weighted Average Price) systems, instead of relying on potentially volatile spot prices [9]. For Layer 2 protocols or those using bridges, auditors confirm the presence of "Escape Hatches" that allow users to withdraw funds if a sequencer or bridge validator is compromised [9].
How to Evaluate Audit Quality and Choose Auditors
Not all audits hold the same level of importance, and the choice of an auditor speaks volumes about a protocol’s maturity and dedication to security. For institutional investors, picking the right audit partner is just as crucial as the audit itself. Here’s how to assess audit quality and select dependable auditors.
Auditor Reputation and Track Record
The DeFi audit landscape is divided into tiers. Tier 1 firms like OpenZeppelin, Trail of Bits, and Spearbit are considered the gold standard, trusted by protocols managing billions in Total Value Locked (TVL). These firms conduct in-depth architectural reviews. On the other hand, elite solo auditors such as Pashov and Trust bring agility and a hands-on approach, ideal for early-stage projects. Crowdsourced platforms like Code4rena and Sherlock also offer a unique model, engaging hundreds of researchers to uncover vulnerabilities, making them a strong choice for high-TVL protocols [11].
"In the investor’s eyes, not all audits are created equal. The smart contract audit services you choose signal your project’s capitalization and your team’s foresight." – Zealynx Security [2]
Steer clear of firms that offer quick, low-cost audits, such as $500 services with 48-hour turnarounds. These "compliance-only" audits often lack substance and indicate a weak commitment to real security [9]. Instead, prioritize firms with observable deliverables, like public audit libraries, disclosed findings, and contest results. High-performing firms often maintain average ratings of 4.7 stars on platforms such as Trustpilot or GitHub, while those with poor track records hover around 2.1 stars [8].
Ask for a threat model that explains roles, trust boundaries, and invariants to better understand the auditor’s methodology. Ensure the audit corresponds to the currently deployed version of the protocol – an audit for an earlier version won’t cover updates. Check commit hashes in the report to confirm that identified issues match the fixes applied [11].
Audit Scope and Coverage
Reputation is important, but the depth of the audit’s scope is equally critical. A high-quality audit should address core business logic, including staking mechanisms, lending pools, vaults, and oracle integrations, rather than limiting itself to standard ERC-20 token features. If the audit’s scope is unclear, it could be a sign of incomplete coverage.
A thorough audit also includes a retest process, where fixes are validated to ensure vulnerabilities are resolved, not just acknowledged. A high number of initial critical bugs (15 or more) may suggest over-reliance on external auditors instead of strong internal testing [11].
Pay attention to vulnerabilities labeled as "Acknowledged." If a report lists High or Critical risks as "Acknowledged" instead of "Fixed", it means the team has chosen to accept significant risks rather than addressing them – a major red flag for institutional investors [2][8]. Comprehensive audits should also incorporate testnet simulations to model real-world attack scenarios, such as $10 million flash loans or price feed manipulations.
How to Read and Interpret Audit Reports
Audit reports typically categorize findings by severity: Critical, High, Medium, and Low. Critical and High vulnerabilities demand immediate attention, and their remediation status is crucial. Issues marked as "Fixed" indicate resolution, while "Acknowledged" suggests unresolved risks. Any unfixed High or Critical issue should raise serious concerns.
Examine admin controls within the report. Robust protocols use multisig wallets (e.g., 3-of-5 configurations) and enforce a timelock of at least 48 hours for critical changes. Relying on a single externally owned account with minting or pausing privileges presents a centralization risk [2].
"Auditor selection is a buyer-side evidence problem. The strongest picks are the ones with inspectable proof of work… not the ones with the most polished case studies." – TechBullion [11]
Check for an active bug bounty program on platforms like Immunefi, with significant payouts (e.g., $50,000 or more). Such programs demonstrate the team’s confidence in their code and provide ongoing security monitoring. Immunefi has reportedly prevented over $25 billion in losses while paying out more than $125 million to ethical hackers [12]. Before committing funds, use simulation tools like Phalcon to test mainnet transactions. This ensures the contract operates as expected, without unexpected reverts or excessive approval demands.
Building a Security Assessment Framework for DeFi Investments
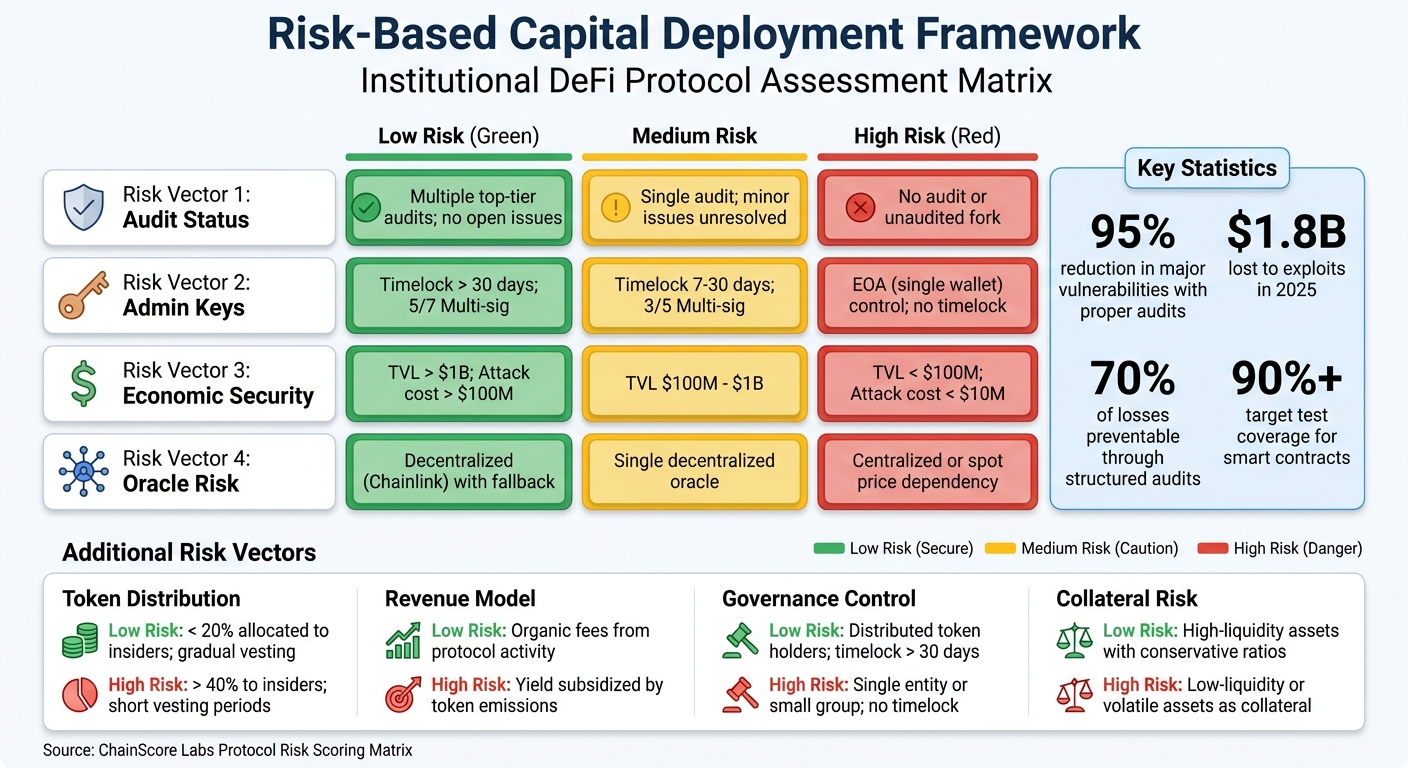
DeFi Protocol Risk Assessment Matrix for Institutional Investors
Institutional investors require a structured method to evaluate DeFi protocols before committing funds. A robust security assessment involves more than just reviewing a single audit report – it calls for multiple layers of verification, ongoing monitoring, and capital allocation based on risk levels. The framework outlined here provides a systematic approach for assessing protocols and making informed investment decisions. It builds on initial audit insights, incorporating continuous monitoring and risk-adjusted strategies.
Complete Audit Coverage
Audit relevance is just as critical as audit quality. A protocol audited at version 1.0 may have undergone major changes by version 3.0, making the original audit outdated. Always verify that the audit matches the current deployment by checking commit hashes on platforms like Etherscan or Sourcify [13].
The audit’s scope determines its effectiveness. It must cover essential components like staking mechanisms, lending pools, vault strategies, and oracle integrations. An audit limited to standard ERC-20 token functionality while ignoring the protocol’s unique mechanisms is insufficient.
All high and critical vulnerabilities must be resolved and marked as "Fixed", with verification through commit hashes. If a report lists critical issues as merely "Acknowledged", it indicates the team has chosen to accept significant risks rather than address them. As Zealynx Security warns, “Unless there is a massive governance constraint (like a Timelock) in place, an unfixed ‘Acknowledged’ risk is a disqualifier” [2].
Target a 90% or higher test coverage for smart contracts and prioritize protocols audited by top-tier firms such as Trail of Bits, OpenZeppelin, Spearbit, or Quantstamp [1].
Bug Bounty Programs and Continuous Monitoring
Audits provide a snapshot of security at a specific time, but protocols evolve, and new vulnerabilities can emerge. Active bug bounty programs hosted on platforms like Immunefi offer ongoing security checks. Look for programs with payouts of $50,000 or more for critical vulnerabilities, as this reflects the team’s confidence in their protocol and attracts skilled whitehat hackers [13]. Immunefi reports that 80% of its clients have received valid disclosures of critical vulnerabilities, preventing over $25 billion in potential losses while paying out more than $125 million to ethical hackers [12].
Real-time monitoring tools are essential for identifying threats before they escalate. Use services like Forta Network or OpenZeppelin Defender to track unusual activity, governance attacks, or suspicious transactions [13]. Set alerts for new governance proposals or significant vote delegations, as these could indicate protocol changes or attempts to drain funds [13].
Leverage on-chain analytics platforms like Nansen, DeFiLlama, and Dune Analytics to monitor Total Value Locked (TVL) trends, revenue patterns, and whale movements. Sudden shifts in TVL or liquidity concentration can signal emerging risks [13]. The Immunefi Foundation stresses the importance of quick action: “Seconds can determine whether funds are lost. This latency is a structural vulnerability” [12].
Continuous monitoring complements periodic audits, ensuring that new threats are detected and addressed promptly.
Risk-Based Capital Deployment
Not all protocols warrant the same level of investment. Allocate funds in proportion to the protocol’s risk profile. Use simulation tools from firms like Gauntlet or Chaos Labs to evaluate how the protocol performs under market stress or flash crashes [13]. Before deploying capital, simulate transactions with tools like Phalcon or Tenderly to confirm expected contract behavior [9].
Evaluate liquidity depth; if the top 10 providers control more than 40% of the supply, risks are elevated [13]. Check how admin keys are managed – protocols should use multi-signature wallets (e.g., 5-of-7 configurations) with timelocks of at least 48 hours, ideally extending to 30 days or more, to prevent immediate malicious changes [13]. A single externally owned account (EOA) controlling critical functions is a major warning sign.
Carefully assess oracle dependencies. Protocols that rely on DEX spot prices are vulnerable to flash loan attacks. Ensure the protocol uses decentralized oracles like Chainlink or Time-Weighted Average Prices (TWAP) [9]. The 2022 Nomad Bridge hack, which led to a $190 million loss, highlights how even minor oversights can result in catastrophic outcomes [13].
| Risk Vector | Low Risk | Medium Risk | High Risk |
|---|---|---|---|
| Audit Status | Multiple top-tier audits; no open issues | Single audit; minor issues unresolved | No audit or unaudited fork |
| Admin Keys | Timelock > 30 days; 5/7 Multi-sig | Timelock 7-30 days; 3/5 Multi-sig | EOA (single wallet) control; no timelock |
| Economic Security | TVL > $1B; Attack cost > $100M | TVL $100M – $1B | TVL < $100M; Attack cost < $10M |
| Oracle Risk | Decentralized (Chainlink) with fallback | Single decentralized oracle | Centralized or spot price dependency |
Source: ChainScore Labs Protocol Risk Scoring Matrix [13]
Non-Technical Risks in DeFi Protocols
When evaluating the resilience of DeFi protocols, it’s important to look beyond technical audits. While these audits confirm code integrity, they often miss critical issues like governance vulnerabilities and flawed token economics. For institutional investors, understanding risks tied to governance structures, decision-making power, and incentive mechanisms is just as important as ensuring the code itself is secure. Even the most secure smart contracts can fail if the underlying economic or governance design is unsound.
Counterparty and Governance Risk Assessment
One of the biggest risks in DeFi stems from who holds the admin keys. A compromised admin key can allow attackers to disable a protocol or steal funds. A stark example occurred in November 2021, when the bZx protocol lost around $55 million after a phishing attack led to the theft of a developer’s private key [14]. Here, the flaw wasn’t in the code but in human vulnerability.
Governance concentration poses another significant challenge. In April 2022, Beanstalk Farms lost $182 million when an attacker exploited a governance loophole. Using a flash loan from Aave, the attacker acquired enough governance tokens (STALK) to pass a malicious proposal and drain the protocol’s funds [14]. This incident highlights how poorly designed governance systems can allow wealthier actors to hijack decision-making.
Even with multisignature (multisig) setups, risks persist. The identity and affiliations of multisig signers matter. If all signers are anonymous or connected to the same entity, the system remains fragile.
Centralized bridge controls are another weak point. For instance, in March 2022, the Ronin Bridge suffered a $624 million loss when attackers compromised the centralized entities managing the bridge contract [14]. This rendered the wrapped assets on the destination chain worthless almost immediately.
DeFi protocols also face compliance risks. Interacting with pools containing funds from sanctioned entities or hacked addresses can create legal exposure. Brian E. Nelson, Under Secretary of the Treasury for Terrorism and Financial Intelligence, warned:
"Our assessment finds that illicit actors, including criminals, scammers, and North Korean cyber actors are using DeFi services in the process of laundering illicit funds" [15].
To mitigate these risks, institutions should use real-time monitoring tools to screen transaction flows and avoid protocols with weak Know Your Customer (KYC) or Anti-Money Laundering (AML) measures.
Protocol Economics and Incentive Structures
A protocol’s long-term viability depends heavily on its economic design. Even perfect code cannot fix broken tokenomics. Economic audits, which assess factors like emission schedules and revenue models, are essential for identifying weaknesses. As Three Sigma explains:
"While a perfectly coded protocol can function flawlessly, it may still fail if its economic design is poorly conceived" [16].
Protocols relying on token emissions to attract liquidity often fall into "farm-and-dump" cycles. In these cases, users farm rewards and sell them immediately, causing token prices to plummet [13]. Instead, sustainable protocols generate revenue through mechanisms like swap fees or lending spreads. If a protocol’s Total Value Locked (TVL) collapses when token emissions stop, it’s a clear sign of economic instability.
Token distribution is another key factor. If insiders (like the team and early investors) control over 40% of the tokens, there’s a high risk of significant sell pressure destabilizing the protocol [13]. Vesting schedules and unlock dates should also be analyzed to predict when large token holders might exit.
Collateral management is critical too. In October 2022, Mango Markets collapsed when a low-liquidity asset used as collateral crashed in value. This left the protocol with bad debt because the borrowed amount exceeded the collateral’s worth [16]. Such failures often result from poorly set parameters, like allowing volatile assets as collateral without adequate safeguards.
Economic vulnerabilities can also emerge from business logic flaws. For example, in January 2022, a Code4rena audit of Sandclock identified a high-risk issue in the forceUnsponsor() function. This flaw could have allowed attackers to manipulate _totalShares and potentially freeze user funds [17]. Economic audits often use tools like backtesting and stress testing to catch these risks before they cause real damage.
| Risk Vector | Low Risk | High Risk |
|---|---|---|
| Token Distribution | < 20% allocated to insiders; gradual vesting | > 40% to insiders; short vesting periods |
| Revenue Model | Organic fees from protocol activity | Yield subsidized by token emissions |
| Governance Control | Distributed token holders; timelock > 30 days | Single entity or small group; no timelock |
| Collateral Risk | High-liquidity assets with conservative ratios | Low-liquidity or volatile assets as collateral |
Source: ChainScore Labs and Three Sigma Risk Frameworks [13][16]
Conclusion
Audits play a critical role in guiding institutional capital deployment. In 2025 alone, $1.8 billion was lost to exploits – 70% of which stemmed from vulnerabilities that could have been avoided with proper audits [10]. Structured audits have the potential to reduce exposure to major vulnerabilities by as much as 95% before mainnet launch [10]. This highlights the importance of integrating strong audit practices into every investment strategy.
A proven track record of rigorous audits not only reduces perceived risk but also enhances capital valuations. As Zealynx Security aptly puts it:
"Founders often view audits as a ‘security tax.’ Investors view them as a ‘valuation multiplier’" [2].
In the Web3 space, bugs often have catastrophic consequences – a single flaw can wipe out an entire protocol in one block [2]. This binary nature of risks makes a robust security stack a non-negotiable requirement for investors. Today, they expect protocols to demonstrate:
- Verified remediation of critical vulnerabilities (marked as "Fixed" rather than "Acknowledged")
- Active bug bounty programs
- Real-time monitoring tools
- Ongoing security partnerships [2]
Additionally, continuous verification ensures that the audited code aligns with the deployed contracts, with a clear preference for audits conducted by Tier-1 firms [2].
Investing in security yields tangible benefits. The return on investment (ROI) can range from 10x to 100x when factoring in avoided losses and reputational damage [5]. By 2026, regulatory frameworks are expected to mandate published audit reports for DeFi protocols catering to institutional investors [10]. Beyond meeting compliance requirements, thorough audits also open doors to Tier-1 exchange listings and DeFi insurance eligibility [1][2].
Institutions that adopt a comprehensive approach to security – addressing both technical vulnerabilities and economic design flaws – are better equipped to navigate the opportunities and risks of DeFi. Protocols that embed security into every stage, from development through deployment, position themselves as leaders in the evolving landscape. By making these practices integral to their investment frameworks, institutions can safeguard their interests while staying ahead of emerging threats.
FAQs
What should I verify to ensure an audit matches the deployed contracts?
To verify that the audit aligns with the deployed contracts, make sure the deployed code matches the audited version exactly. Pay close attention to the consistency of the code, logic, and any changes or fixes made during the audit. This step is crucial to ensure the implementation adheres to the security and compliance standards outlined in the audit.
Which unresolved audit findings are deal-breakers for institutions?
Unresolved audit findings that institutions consider deal-breakers often involve major vulnerabilities, such as reentrancy attacks, logic errors, improper access controls, and oracle manipulation. These flaws can lead to severe financial losses or manipulation of funds if left unaddressed before deployment. To safeguard their investments and ensure the security of DeFi protocols, institutions focus heavily on resolving these risks.
How do I assess non-technical risks like governance and tokenomics?
When assessing non-technical risks, it’s essential to take a closer look at governance structures and tokenomics. Start by analyzing whether the protocol’s economic model encourages long-term value creation. Does the tokenomics design align with sustainable growth, or does it rely on short-term incentives that could lead to instability?
Next, consider the adaptability of governance mechanisms. Can they effectively respond to evolving challenges or unforeseen issues? A well-designed governance system should be flexible enough to address changes without compromising the protocol’s core values.
Finally, evaluate the protocol’s risk management and operational practices. These can provide insight into the quality of governance and the team’s ability to maintain resilience under pressure. Unlike technical audits, this broader review focuses on ensuring the protocol meets institutional expectations and can weather potential disruptions.