Cross-chain smart contracts allow blockchains to communicate, enabling assets and data to move between networks like Ethereum, Avalanche, and Polygon. This solves liquidity fragmentation, where assets are trapped in isolated ecosystems, and improves efficiency by linking these networks. For example, Aave used this in January 2026 to synchronize governance and enable stablecoin transfers using Chainlink CCIP.
Key takeaways:
- How it works: Uses messaging protocols and relayers to transfer data and assets securely.
- Benefits: Reduces inefficiencies like slippage and splits in liquidity pools.
- Core components: Includes paired source/destination contracts, messaging protocols, and cross-chain tools like Chainlink CCIP and LayerZero.
- Applications: Powers decentralized exchanges, tokenized asset transfers, and Layer 2 integrations.
- Challenges: Security risks, gas volatility, and liquidity fragmentation are addressed with solutions like unified pools and multi-layer verification.
Cross-chain smart contracts are reshaping blockchain by connecting networks into a single ecosystem, making operations smoother and more efficient while addressing security and liquidity issues.
Core Components of Cross-Chain Smart Contracts
Source and Destination Chain Contracts
These contracts are the backbone of cross-chain interactions, ensuring smooth operations between networks.
On one side, the source chain contract initiates the process. When a user triggers a cross-chain action, this contract bundles data, tokens, and commands into a message payload. It also handles asset transfers using mechanisms like "Lock" or "Burn", ensuring the total supply of assets remains consistent across networks [3][6][7]. Once the payload is ready, the contract emits an on-chain event, signaling off-chain relayers to step in [6][7].
On the other end, the destination chain contract takes over as the verifier and executor. It confirms the authenticity of the source transaction using cryptographic proofs provided by relayers [3][6]. To maintain security, it processes messages only if they originate from authorized sources [9]. Once validated, the contract decodes the payload and executes its instructions. This could involve minting tokens, updating state variables, or even activating specific DeFi operations [3][9].
Together, these paired contracts set the stage for a multi-step messaging process, detailed below.
Messaging Protocols and Relayers
Messaging protocols ensure secure and standardized communication between chains through a three-stage process:
- Origin: The source chain emits an event.
- Transport: Off-chain entities (relayers) validate and relay the message.
- Destination: The target chain verifies and executes the command [3][6].
Relayers play a critical role here. These off-chain entities monitor events on the source chain, capture signed messages or proofs, and deliver them to the destination chain’s smart contracts [6][11].
For added security, these protocols often use validators or oracles to confirm that transactions on the source chain have reached finality before relaying them. Advanced systems also monitor for irregularities, such as attempts to mint more tokens than were locked [6][12]. Protocols like Allbridge Core employ "Hashed Messaging", which compresses data payloads into 32-byte fingerprints, reducing both storage and gas costs [11].
Cross-Chain Protocols
Several protocols have been developed to make cross-chain communication more reliable and efficient, each offering unique approaches:
- Chainlink CCIP combines Decentralized Oracle Networks with a risk management system to detect anomalies. By 2025, it had processed $7.77 billion in transactions, marking a 1,972% increase from the previous year [6][10][12].
- LayerZero uses an "Ultra Light Node" design, where independent oracles and relayers collaborate to finalize transactions in under 30 seconds. It currently connects over 150 blockchains and has handled more than 150 million messages [5][10].
- In the Cosmos ecosystem, the Inter-Blockchain Communication (IBC) protocol relies on light clients and relayers, with native support on both chains. As of August 2024, IBC connected 78 zones and earned a security score of 91/100 from Trail of Bits, the highest among major protocols [5][13].
- Wormhole employs a guardian network of 19 validators to verify transfers. It processes over $300 million in daily volume across 35–40 connected chains [10].
Each protocol comes with its own trade-offs in terms of speed, security, and cost. For instance, transaction fees can range from $0.02 for IBC to $2.85 for enterprise-level setups with CCIP [5].
sbb-itb-c5fef17
Chain Abstraction Educate: Writing Asynchronous, Cross-Chain Smart Contracts Using Agoric
Step-by-Step Guide to Deploying Cross-Chain Smart Contracts
How Cross-Chain Smart Contracts Work: 4-Stage Process Flow
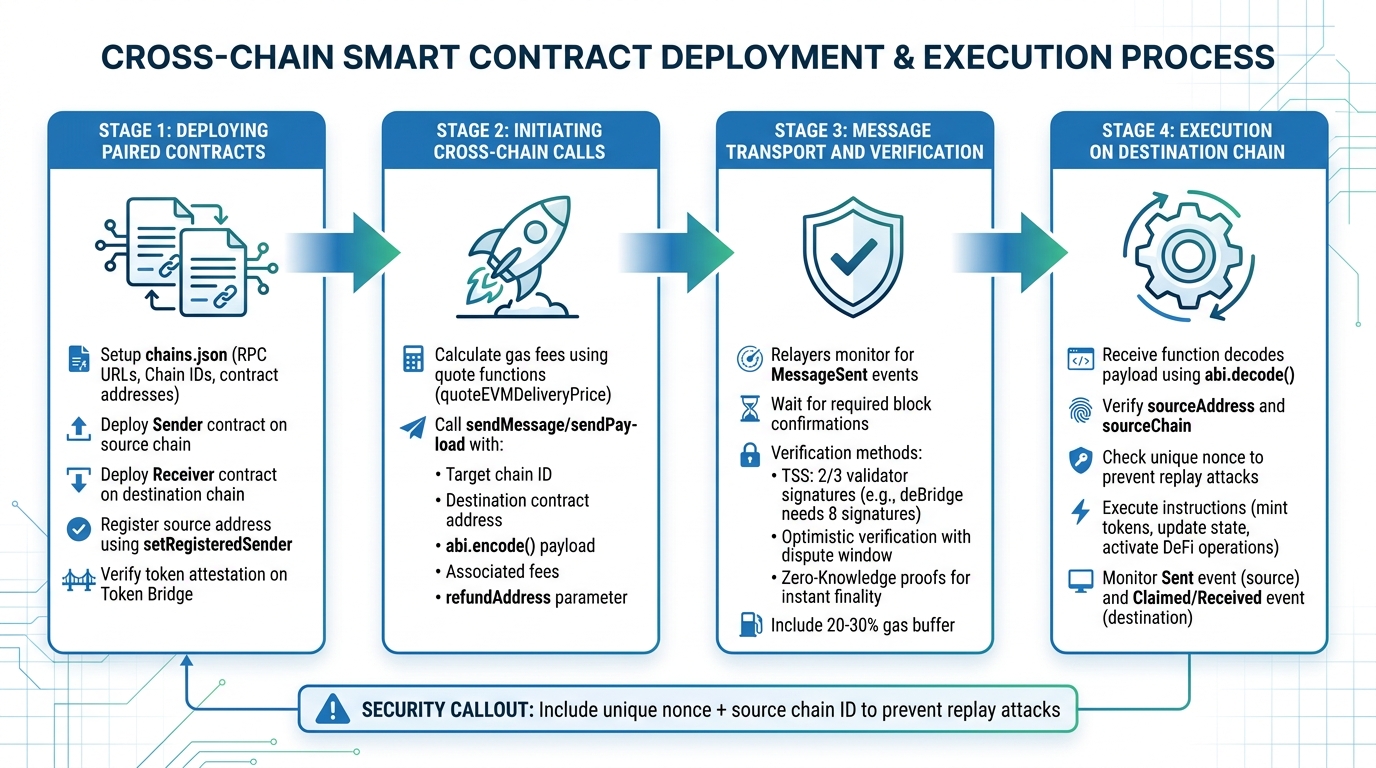
Deploying Paired Contracts
Start by setting up your environment with a configuration file, such as chains.json. This file should include critical details like RPC URLs, Chain IDs, and key contract addresses for each network you’re working with. These addresses typically include the messaging relayer, token bridge, and core protocol components [14][15].
Next, deploy the Sender contract on the source chain and the Receiver contract on the destination chain. These contracts often extend SDK-provided abstract classes like TokenSender and TokenReceiver, which simplify much of the process [15]. Use tools like Foundry or Hardhat to deploy the contracts individually – for instance, deploying the sender to Avalanche and the receiver to Base [14].
To ensure security, register the source contract’s address in the destination contract using methods like setRegisteredSender. This step ensures the receiver only processes messages from your authorized paired contract on the source chain [14][15]. When registering addresses, use ethers.zeroPadValue to convert the standard 20-byte EVM address into the 32-byte format required by most cross-chain protocols [14][15].
For token-related contracts, confirm that your token has an attestation on the Token Bridge of the destination chain. Without this attestation, the transfer will fail because the wrapped version of the token cannot be minted [15].
Initiating Cross-Chain Calls
Once your paired contracts are deployed and emitters registered, you can begin initiating cross-chain calls. Start by calculating the gas fees required on the destination chain. Use protocol-specific quote functions like Wormhole’s quoteEVMDeliveryPrice or deBridge’s executionFee to get real-time pricing [14][17][15]. These fees typically include the deliveryCost (gas for the destination chain) and a messageFee (protocol-specific fee) [14][15].
You can then call methods like sendMessage or sendPayload with the required parameters, including the target chain ID, destination contract address, abi.encode() payload, and associated fees. Many protocols also require a refundAddress parameter to return any unused gas if the actual execution costs are less than the quoted amount [17][18].
Message Transport and Verification
Once the cross-chain call is initiated, decentralized relayer networks step in to monitor the source chain for events like MessageSent. These relayers retrieve cryptographic proofs and submit them to the destination chain. Before processing messages, they wait for the required block confirmations [17].
Message verification depends on the protocol. For instance:
- Threshold Signature Schemes (TSS) rely on a super-majority (typically two-thirds) of validators to sign a message. deBridge, for example, requires at least eight validator signatures representing two-thirds of the set for confirmation [17][16].
- Optimistic verification assumes messages are valid unless they are challenged during a dispute window.
- Zero-Knowledge proofs provide instant finality but come with higher computational demands [16].
These verification methods work seamlessly with your deployed contracts, maintaining a secure cross-chain setup.
"The core challenge is creating a trust-minimized system where relayers cannot censor, delay, or tamper with messages without being penalized." – ChainScore Labs [16]
To account for execution variability, include a 20–30% gas buffer and use eth_estimateGas to simulate execution costs before submitting a transaction [16].
Execution on the Destination Chain
Once the message is verified, the destination chain executes the payload. The destination contract’s receive function decodes the payload using abi.decode() and performs the instructions. It first verifies the message’s authenticity by checking the sourceAddress and sourceChain parameters to ensure the sender is registered [14][15][18].
To prevent replay attacks, include a unique nonce and the source chain ID in every message payload. This ensures the message cannot be reused on other chains or executed multiple times on the same chain [16]. Additionally, track message IDs in a database to avoid duplicate relays, which could lead to fund depletion [16].
Monitor the transaction’s progress by observing the Sent event on the source chain and the Claimed or Received event on the destination chain [17]. If you’re using LayerZero, the NonblockingLzApp interface can help prevent a single failed message from blocking the entire communication channel [18].
Challenges and Solutions in Cross-Chain Smart Contracts
When it comes to cross-chain smart contracts, the challenges go far beyond just deploying them. Managing risks like chain reorganizations and liquidity fragmentation is crucial to ensure smooth and secure interactions across networks. These issues impact security, performance, and user experience, and this section dives into the key challenges and the strategies used to address them.
Chain reorganizations are a significant risk. Imagine a situation where a bridge processes a transaction, but then the source chain undergoes a reorganization. This could reverse the transaction, leading to problems like double-spending or inconsistent states between networks. To counter this, it’s essential to wait for deep finality before triggering actions on the destination chain [19][20].
Security vulnerabilities are another major concern. Cross-chain bridges have been frequent targets of attacks, with devastating consequences. For example, the Wormhole bridge suffered a $325 million exploit in February 2022 due to a flaw in signature verification. Since 2020, such attacks have caused over $2.5 billion in losses [20][5]. To reduce these risks, several measures can be employed: multi-layered defenses with independent verification layers, automated circuit breakers to pause operations during suspicious activities, and rate limiting to restrict the maximum value that can be extracted over a specific period. As security researcher Samczsun aptly put it:
All cross-chain bridges represent concentrated attack surfaces [5].
Liquidity fragmentation is another obstacle. When assets are locked in isolated pools, it leads to inefficient use of capital and higher slippage during transactions. Solutions include unified liquidity pools, such as Stargate, and intent-based architectures that use competitive solvers to simplify cross-chain complexity [20][2]. Meanwhile, gas volatility poses challenges for multi-step calls, especially during price spikes or network congestion. Addressing this involves implementing gas abstraction mechanisms and off-chain retry relayers to manage the unpredictability of gas prices [20].
Challenges and Mitigations Table
Here’s a quick overview of the challenges and their solutions:
| Challenge | Technical Solution | Operational Mitigation |
|---|---|---|
| Chain Reorganizations | Finality depth monitoring | Optimistic challenge periods |
| Liquidity Fragmentation | Unified liquidity pools (e.g., Stargate) | Intent-based solver networks |
| Heterogeneous Consensus | Custom light client logic | Standardized messaging (IBC/CCIP) |
| Validator Collusion | Multi-layer verification networks | Anti-fraud monitoring DONs |
| Gas Volatility | Gas abstraction/pre-payment | Off-chain retry relayers |
These strategies aim to tackle the technical and operational hurdles in cross-chain smart contracts, ensuring more secure, efficient, and reliable interactions across blockchain networks.
Real-World Applications of Cross-Chain Smart Contracts
Practical examples highlight how cross-chain techniques are addressing key challenges in blockchain ecosystems.
Cross-Chain Decentralized Exchanges (DEXs)
Cross-chain DEXs are revolutionizing trading by merging liquidity pools that were once isolated. This reduces slippage and ensures better pricing for users. Modern DEXs combine bridging and swapping into a single, seamless process, removing the need for manually bridging assets [21].
Intent-based systems take this a step further by simplifying multi-chain interactions. For instance, users can specify something like, "I have ETH on Mainnet and want USDC on Arbitrum", and a network of solvers competes to fulfill the request at the best price [21]. As CoW DAO explains:
The industry is trending toward ‘chain abstraction,’ where the user no longer needs to know which blockchain their assets are on [21].
Adoption of these technologies is accelerating. In Q2 2024, cross-chain transactions surpassed $25.7 billion, and by 2025, DEX monthly trading volumes averaged $412 billion [5][22]. Additionally, LayerZero supported 83% of cross-chain NFT projects by May 2024, while Chainlink CCIP captured 67% of the institutional cross-chain transaction market by June 2024 [5].
These advancements naturally lead into how tokenized assets are securely transferred across blockchains.
Tokenized Asset Transfers
Securely moving tokenized assets between blockchains requires precise coordination between smart contracts. A notable example occurred in June 2024, when Circle used Chainlink CCIP’s burn-and-mint system to enable native USDC transfers between Ethereum and Solana. This approach preserved the total supply without relying on locked liquidity pools [5].
Institutional players are also leveraging these innovations. In 2024, J.P. Morgan’s Kinexys platform and Ondo Finance showcased atomic cross-chain Delivery vs. Payment (DvP) transactions. These ensure that asset delivery and payment occur simultaneously, eliminating counterparty risk [2][23].
The scale of these transfers is staggering – over $1.3 trillion in tokenized assets had been moved across chains via bridges by late 2025 [1]. Security measures like Hash Time-Locked Contracts (HTLCs) ensure that trades either complete fully or fail entirely, while rate-limiting mechanisms restrict token transfer volumes within specific timeframes.
These techniques enhance the reliability of asset transfers and strengthen cross-chain interoperability, setting the stage for even more sophisticated applications.
Integration with Layer 2 Solutions
Cross-chain smart contracts are also bridging the divide between Layer 1 (L1) security and Layer 2 (L2) efficiency. Developers can run high-frequency operations on more economical L2 networks while maintaining critical asset tracking on secure L1 blockchains [8][3].
In June 2024, Axelar Network introduced "GMP+" (General Message Passing Plus), cutting gas costs for cross-chain smart contract calls by 95%. DeFi platform Aave quickly adopted this innovation to efficiently move liquidity between Ethereum and Avalanche [5]. By 2025, Chainlink CCIP enabled Coinbase to manage $7 billion in wrapped Bitcoin operations, facilitating secure transfers between Ethereum L1 and Coinbase Base L2 [10].
The numbers tell the story: Chainlink’s Cross-Chain Interoperability Protocol processed $7.77 billion in 2025, marking a 1,972% year-over-year increase [10]. Institutions are increasingly capitalizing on L1–L2 integration for atomic settlements and data synchronization, with Ethereum acting as the central hub – 87% of protocols connect to it [5].
Conclusion and Key Takeaways
Cross-chain smart contracts are reshaping blockchain interactions by connecting isolated networks into a unified ecosystem. Their operation revolves around a three-stage process – initiation, validation, and execution – which requires seamless coordination between sender contracts, messaging protocols, and receiver contracts[3].
Security is the cornerstone of this technology. As Chainlink emphasizes:
The security of the cross-chain application is effectively equal to the security of the least secure chain or the messaging protocol used.[3]
Given that over $1.3 trillion in token transfers have occurred[1], developers should rely on trusted protocols like Chainlink CCIP or IBC. Implementing robust authorization checks is critical to ensure receiver contracts only process messages from verified sources. Additionally, waiting for deep finality on source chains before executing transactions can prevent vulnerabilities.
The industry is evolving toward chain abstraction, which allows users to focus on desired outcomes rather than manually managing bridges. Standards like ERC-7683 are helping unify the ecosystem, while burn-and-mint mechanisms are proving more capital-efficient than traditional lock-and-mint models[4].
On-chain functions also play a key role by dynamically quoting fees and setting gas limits for destination execution[9]. Cross-chain capabilities are driving advancements in areas like DeFi liquidity aggregation, tokenized asset transfers, and the integration of Layer 1 and Layer 2 networks. Developers can now design hub-and-spoke architectures that keep critical logic on secure chains while using faster, lower-cost networks for high-frequency operations.
Choosing the right messaging protocol is a pivotal decision. For example, IBC offers a high security score (91/100) and low transaction costs (around $0.02), while LayerZero provides quicker finality – under 30 seconds – with fees ranging from ~$0.10 to $1.50 per transaction[5]. Addressing finality mismatches and deploying monitoring tools to track transaction statuses are also essential for building secure and efficient cross-chain solutions.
These insights highlight the strategic decisions and technical considerations developers need to navigate when implementing cross-chain smart contracts. By understanding these elements, teams can create robust systems that balance security, efficiency, and functionality.
FAQs
What’s the safest way to pick a cross-chain messaging protocol?
When selecting a secure cross-chain messaging protocol, focus on options that emphasize strong security measures, proven reliability, and active community involvement. Key features to look for include:
- A solid infrastructure that can handle complex transactions.
- The use of cryptographic proofs to ensure data integrity.
- Completion of thorough audits to identify and address vulnerabilities.
For added protection, consider protocols that offer multi-signature validation or similar safeguards. By carefully evaluating these aspects, you can ensure a safer and more dependable cross-chain communication experience.
How do I prevent replay attacks in cross-chain smart contracts?
To guard against replay attacks in cross-chain smart contracts, it’s essential to implement a nonce or a unique transaction identifier within the signed message. This ensures that each signature can only be used once. Another key step is binding signatures to specific chain IDs and contract addresses, restricting their usage to a particular context. Additionally, keep a log of all used nonces or signatures to prevent any attempt at reuse. These measures collectively strengthen the protection of smart contracts against replay attacks.
How do cross-chain apps handle gas spikes and failed destination execution?
Cross-chain apps tackle issues like gas spikes and failed destination execution by using transaction tracking, error handling, and retry systems. For example, tools such as Axelar’s SDK enable users to keep an eye on transactions, spot potential problems, and either resubmit or approve them as needed. Additionally, protocols can modify gas parameters or relay transactions to recover from failures. These techniques work together to ensure transactions are successfully completed across multiple chains, even when gas-related challenges arise.


