Decentralized storage networks rely on independent providers to store data securely without central control. This setup distributes risk across participants but requires strong incentives to ensure providers store data honestly. Three main models address this:
- On-Chain Verification: Uses blockchain-based cryptographic proofs like Proof-of-Replication (PoRep) and Proof-of-Spacetime (PoSt) to verify storage. While reliable, it’s costly and has scalability challenges.
- Off-Chain Audits: Reduces costs by relying on peer-to-peer or external audits. However, it risks dishonesty since auditors might falsely claim compliance.
- Hybrid Models: Combines off-chain audits with random on-chain checks to balance cost and reliability. For example, the Shelby protocol uses erasure coding and penalties for dishonest behavior, ensuring providers meet their obligations.
Each model has trade-offs between cost, scalability, and reliability. Hybrid models, like Shelby, aim to strike a balance, making them suitable for large-scale networks. The key is aligning economic incentives to promote honest participation while keeping costs manageable.
Walrus Protocol Is The FUTURE of Decentralized Storage!
sbb-itb-c5fef17
1. On-Chain Verification Models
On-chain verification models rely on blockchain-based cryptographic proofs to confirm that storage providers are storing their assigned data. Two key proofs are Proof-of-Replication (PoRep), which ensures that a unique copy of data is stored, and Proof-of-Spacetime (PoSt), which verifies that the data remains stored continuously over a specific period [5]. Filecoin serves as a practical example of how these models function within a decentralized storage network.
In the Filecoin network, storage providers must submit PoSt proofs every 24 hours using a mechanism called WindowPoSt. To participate, providers must post collateral upfront, which includes PreCommit and Initial Pledge deposits. Additionally, they need to maintain at least 10 TiB of raw storage power to qualify for block rewards. Missing proof submissions results in fault fees, and rewards are divided into two parts: storage fees paid by clients and block rewards. The block rewards are further split, with 25% released immediately and 75% locked for 180 days [4].
While these on-chain methods ensure robust verification, they come with high costs and scalability challenges. As Michael Crystal, Guy Goren, and Scott Duke Kominers note:
"A trivial solution – auditing every action on-chain – is prohibitively expensive" [1].
This highlights the challenge of balancing thorough verification with the limitations of blockchain resources. To address these issues, the Shelby protocol, developed by Aptos Labs and Jump Crypto in October 2025, introduces a two-tiered audit system. In this approach, providers perform multiple off-chain audits per epoch, while the blockchain randomly verifies certain reports using Merkle inclusion proofs. This method allows for:
"infrequent but perfectly verifiable audits" [1].
If an auditor fails to provide the required cryptographic proof during verification, they face severe slashing penalties. Additionally, storage providers earn rewards based on their performance (calculated as γᵢ · r_st per chunk). Providers with scores below 1 are subjected to extra on-chain verification. The protocol also employs erasure coding (k = 10), which increases data-reconstruction costs by roughly 2.5 times [1].
2. Off-Chain Audit Models
Off-chain audit models aim to cut down on on-chain costs and enhance scalability. Instead of logging every storage proof on-chain, these systems rely on alternatives like peer-to-peer auditing, where storage providers verify each other, or dedicated nodes that check data retention. The main challenge? Ensuring the auditors themselves are trustworthy [1].
In peer-to-peer setups, storage providers directly audit one another. The blockchain introduces public randomness to pick specific data chunks for verification. The audited provider then supplies a Merkle inclusion proof to confirm the data’s existence [1]. Storj V3, however, takes a different route. It uses "Satellites", which are coordinating nodes that perform random checks by downloading small erasure shares to validate data integrity. Storj Labs explained this in December 2018:
"By auditing small random chunks of the actual data, we have access to an infinite number of challenges without generating and maintaining extra information like the Merkle tree proofs" [6].
Storj’s system applies the Berlekamp-Welch algorithm to identify corrupted data and maintains reputation databases off-chain to monitor node performance [6]. This setup replaced the earlier V2 model, which relied on pre-generated challenge-response pairs – an approach that allowed nodes to pass audits without actually storing the full data. While these off-chain methods are cost-efficient, they come with their own set of hurdles.
One major issue with purely off-chain models is the risk of dishonest behavior. Without strict checks, auditors could falsely claim compliance, potentially leading to a breakdown in the system’s integrity. Researchers call this problem "universal shirking", where nodes neither store data nor conduct audits but still report successful compliance [1]. Michael Crystal, Guy Goren, and Scott Duke Kominers highlighted this risk in their October 2025 analysis:
"A mechanism that relies solely on off-chain audits by storage providers (SPs) offers no guarantee that audits are conducted truthfully. Without a way to verify or enforce audits, SPs have a dominant strategy to avoid audit costs and simply report successful outcomes" [1].
To address this vulnerability, hybrid models combine off-chain audits with occasional on-chain verifications. For instance, the Shelby protocol randomly selects a portion of audit reports for blockchain verification with a probability $p_{au}$. Auditors who fail to provide cryptographic proof face severe penalties. This two-layered system encourages honest behavior by making it economically smarter to conduct real audits while keeping the majority of activity off-chain [1]. By blending these methods, networks can strengthen reliability and incentivize high-performing nodes.
3. Hybrid Incentive Models
Hybrid models merge low-cost off-chain audits with on-chain verification to create a more efficient system. In October 2025, researchers Michael Crystal (Stanford), Guy Goren (Aptos Labs), and Scott Duke Kominers (Harvard/a16z) analyzed the Shelby protocol, which was developed by Aptos Labs and Jump Crypto, as part of a new thesis investing model. Their findings showed that this two-tiered system ensures full incentive compatibility for both storage and auditing. By using erasure coding with a 10-chunk threshold, the protocol reduces storage overhead to 50%, a notable improvement compared to traditional replication methods [1].
These models rely on randomness to function effectively. Providers conduct peer audits off-chain, while a random subset of these audits is verified on-chain with a probability of $p_{au}$. If an auditor fails to provide a cryptographic proof – like a Merkle inclusion proof – they incur a slashing penalty of $t_{au}$. This approach combines elements from prior on-chain and off-chain methods. Crystal, Goren, and Kominers elaborated on the economic rationale behind this model:
"The key economic insight… is that infrequent but perfectly verifiable audits are sufficient to enforce truthful auditing off-chain; this in turn means that failures of storage provision will be detected and properly penalized" [1].
Audit scores, based on aggregated peer reports, determine each provider’s share of storage rewards ($r_{st}$). Meanwhile, auditors receive a fixed reward ($r_{au}$). To ensure the system remains fair, slashing penalties must exceed $\bigl(\frac{1-p_{au}}{p_{au}}\bigr)r_{au}$.
The protocol also incorporates additional safeguards to maintain system integrity. Forensics-based slashing, rather than majority voting, deters misbehavior. If a node’s audit score falls below a certain threshold, it triggers extra on-chain storage audits. The system can withstand up to 50% of nodes colluding, provided collusion during audits is prevented. To further reduce collusion risks, auditors may be required to submit vector commitments, such as Merkle tree roots, alongside their reports. This reinforces the focus on incentivizing high-performing nodes.
This design not only addresses scalability but also aligns with earlier discussions on verification challenges. In real-world systems, the cost ratio of storage to reading ($c_{st}/c_{r}$) is about 2.5, making local data storage more cost-effective than reconstructing it during audits. With audit frequencies exceeding three times per month, the system ensures reliability while keeping most operations off-chain. For instance, Swarm separates rewards for storage (disk space) from those for bandwidth (data relay), improving operational efficiency [1][2].
Comparison of Strengths and Weaknesses
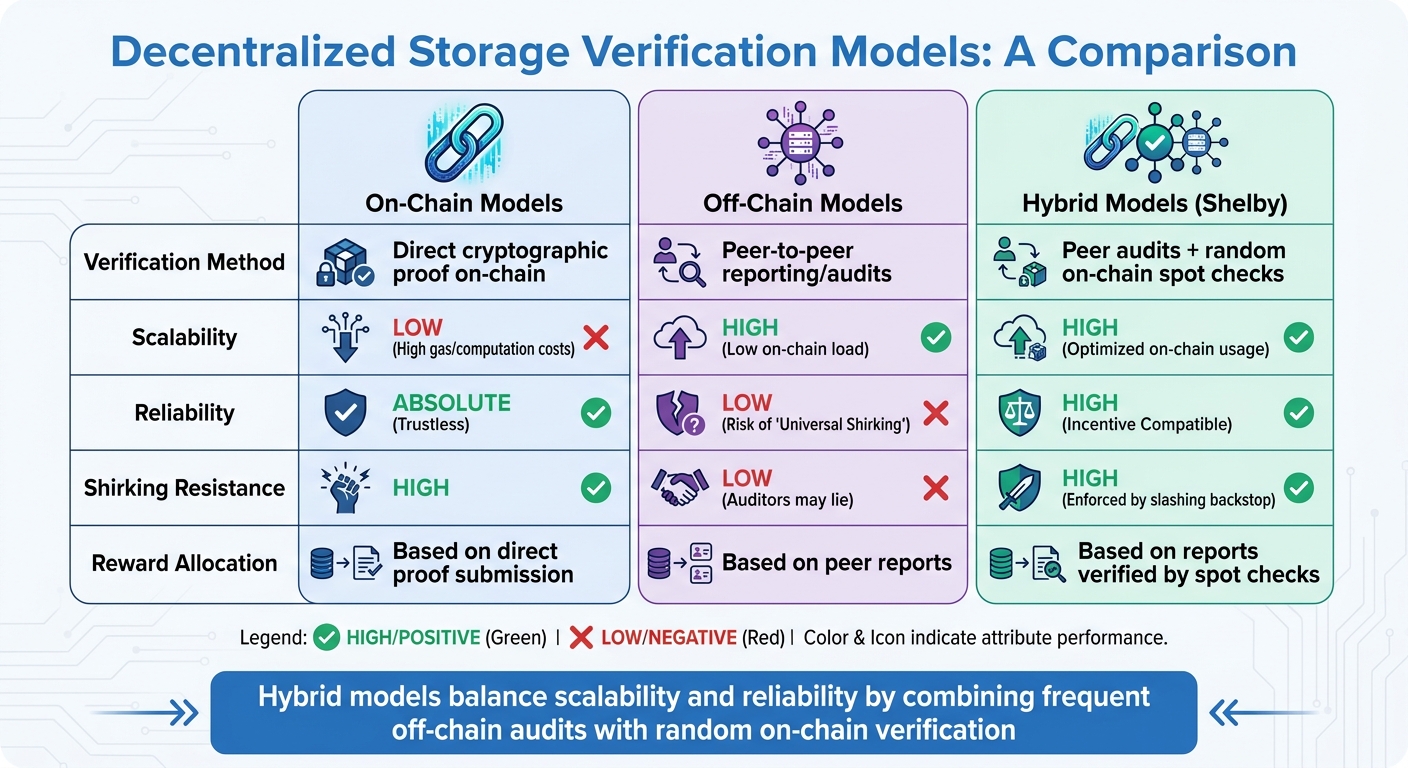
Comparison of Decentralized Storage Verification Models: On-Chain vs Off-Chain vs Hybrid
Each storage verification model balances trade-offs between verification costs, scalability, and resistance to malicious behavior. On-chain verification provides unmatched trust by relying on direct cryptographic proofs. However, the high gas fees and computational demands make it impractical for large-scale storage networks. Off-chain models, while cost-efficient and scalable, face the risk of a "universal shirking" scenario, where participants collude to falsely report compliance without actually storing data or conducting audits [1].
Hybrid models, such as Shelby, aim to bridge this gap. They combine frequent off-chain peer audits with random on-chain spot checks, offering a balance of scalability and resistance to shirking. This two-layered approach ensures better reliability while keeping costs manageable. The design of incentives in these models not only influences audit accuracy but also determines how rewards are distributed within the network. To better understand the trade-offs, let’s compare these models side by side:
| Feature | On-Chain Models | Off-Chain Models | Hybrid Models (Shelby) |
|---|---|---|---|
| Verification Method | Direct cryptographic proof on-chain | Peer-to-peer reporting/audits | Peer audits + random on-chain spot checks |
| Scalability | Low (High gas/computation costs) | High (Low on-chain load) | High (Optimized on-chain usage) |
| Reliability | Absolute (Trustless) | Low (Risk of "Universal Shirking") | High (Incentive Compatible) |
| Shirking Resistance | High | Low (Auditors may lie) | High (Enforced by slashing backstop) |
| Reward Allocation | Based on direct proof submission | Based on peer reports | Based on reports verified by spot checks |
The differences in these models highlight how critical it is to align incentives with the network’s scale and reliability needs. For example, Shelby rewards participants based on a combination of data volume and audit scores, encouraging consistent performance. Swarm, in contrast, uses a probabilistic "winner-takes-all" reward system, where payouts are influenced by the amount of stake held. This approach may inadvertently favor wealthier nodes [1][3].
The overarching challenge for all these models is ensuring that reconstruction costs for lost data exceed the cost of honest local storage. This economic principle is key to promoting honest behavior as the default strategy across the network.
Conclusion
Selecting the right incentive model for decentralized storage boils down to understanding your network’s specific needs and priorities. On-chain verification offers strong cryptographic trust with direct proofs, but its high costs make continuous verification impractical, limiting its use to occasional spot checks. Meanwhile, off-chain audits provide scalability and cost efficiency but risk falling into "universal shirking" without proper safeguards[1]. These trade-offs open the door to hybrid approaches that aim to combine the best of both worlds.
Hybrid models, like Shelby and Swarm, merge off-chain audits with random on-chain checks to balance efficiency and reliability. This approach directly addresses the cost-versus-reliability dilemma. As Michael Crystal, Guy Goren, and Scott Duke Kominers highlight:
"The key economic insight… is that infrequent but perfectly verifiable audits are sufficient to enforce truthful auditing off-chain; this in turn means that failures of storage provision will be detected and properly penalized"[1].
Shelby, for instance, ensures long-term economic sustainability by making local data storage more cost-effective than reconstructing it from peers. It uses erasure coding that requires at least two-thirds of storage providers to faithfully serve data chunks, achieving a storage-to-reading cost ratio of approximately 2.5:1[1]. Swarm, on the other hand, employs a dynamic price oracle that adjusts storage costs to maintain redundancy, ensuring that the costs of retrieval and reconstruction surpass those of local storage[3].
To further enhance your network’s incentive structure, consider integrating tools like vector commitments (e.g., Merkle roots) with audit reports to deter collusion. Calibrating slashing penalties to outweigh potential rewards, even when adjusted for inspection probabilities, can also strengthen reliability. Additionally, employing erasure coding allows for fault tolerance with roughly 50% overhead, a significant improvement over the 300% or more required by full replication. Each of these measures aligns economic incentives with dependable data storage, contributing to overall network stability.
Ultimately, there’s no one-size-fits-all solution. The best protocol is the one that aligns with your specific workload and scale requirements, ensuring both efficiency and reliability.
FAQs
When should a storage network use on-chain proofs instead of audits?
A decentralized storage network benefits from using on-chain proofs in situations where constant verification is either too expensive or introduces potential security risks. By shifting to a model where verification happens only when specifically requested by clients, the network can maintain incentive compatibility while keeping operational costs low and reducing unnecessary burdens.
How do hybrid audits prevent auditors from lying off-chain?
Hybrid audits leverage on-chain mechanisms, such as succinct data structures and blockchain-based proofs, to ensure both data integrity and accountability. By incorporating these methods, they significantly reduce dependence on off-chain trust, which helps lower the chances of auditors engaging in dishonest practices.
How do you safely choose audit probability and slashing penalties?
To make informed decisions about audit probability and slashing penalties, it’s essential to design mechanisms that strike a balance between minimizing false positives and effectively deterring malicious behavior. Key considerations include factors like fault fees, sector penalties, and consensus fault slashing. These should be adjusted based on the network’s operational history and reliability metrics, similar to how systems like Filecoin approach the issue. This approach helps ensure that penalties remain fair while safeguarding the overall integrity of the network.