Yield farming offers high returns, but the risks are equally high – especially for institutional investors. From reentrancy attacks to flash loan exploits, vulnerabilities in smart contracts have led to billions in losses. In 2023 alone, $3.4 billion was stolen, and the interconnected nature of DeFi means a single exploit can ripple across entire ecosystems.
Key Takeaways:
- Common Risks: Reentrancy attacks, oracle manipulation, flash loan exploits, and governance token vulnerabilities dominate losses.
- Notable Incidents: Euler Finance lost $197M (2023) and Kelp DAO suffered a $292M exploit (2026).
- Tools for Risk Assessment: CertiK Skynet, OpenZeppelin Defender, Slither, Mythril, and Echidna help identify vulnerabilities.
- Risk Mitigation: Multi-audit requirements, timelocks, automated wallets, and real-time monitoring are critical for reducing exposure.
- Institutional Approach: Structured capital allocation (core, satellite, opportunistic), governance safeguards, and continuous monitoring ensure better protection.
For institutions, the focus has shifted from chasing high APYs to prioritizing risk-adjusted returns. By combining thorough technical reviews, real-time monitoring, and disciplined portfolio strategies, investors can navigate DeFi risks more effectively.
Smart Contract Audits, Security, and DeFi FULL Course | Learn smart contract auditing
sbb-itb-c5fef17
Common Smart Contract Vulnerabilities
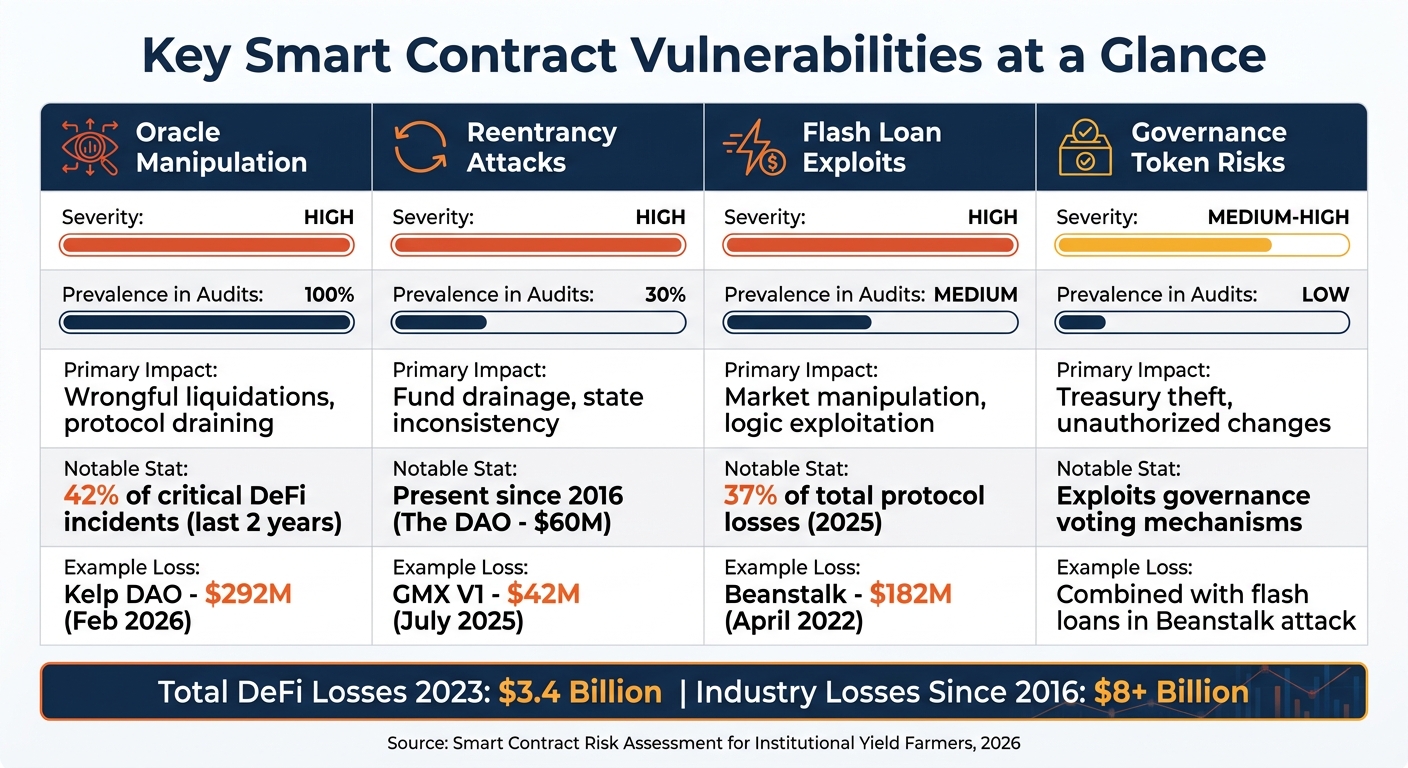
Smart Contract Vulnerabilities: Severity, Prevalence, and Impact Comparison
Since 2016, vulnerabilities in smart contracts have cost the blockchain industry over $8 billion [9]. The numbers are staggering, with $3.4 billion stolen in 2025 alone [10]. These losses highlight the urgent need to address persistent flaws in decentralized finance (DeFi) systems.
Reentrancy Attacks
Reentrancy attacks have been a persistent issue in DeFi, causing significant financial damage. This vulnerability arises when a contract makes an external call to another contract before updating its internal state. The receiving contract can then repeatedly call back into the original function, exploiting outdated data to drain funds. Despite being well-documented since The DAO hack in 2016 – which resulted in the loss of 3.6 million ETH (about $60 million at the time) [12] – reentrancy flaws still show up in 30% of smart contract audits as of 2026 [7].
Modern variations, like cross-function and read-only reentrancy, make these attacks even more dangerous. For example, in July 2025, GMX V1 suffered a $42 million loss when an attacker exploited a reentrancy flaw in the executeDecreaseOrder function. This allowed manipulation of key metrics such as global average short prices and AUM valuations, all due to state updates occurring after external calls. The issue was traced back to a 2022 unaudited patch [6]. Similarly, Curve Finance lost $70 million in July 2023 because of a read-only reentrancy bug in a Vyper compiler that compromised the get_virtual_price() view function [12].
"Reentrancy has been DeFi’s most consistent killer for nearly a decade. The CEI pattern and reentrancy guards make it entirely preventable." – Kennedy Owiro, Founder & CTO, Vultbase [12]
Flash Loan Exploits
Flash loan exploits take advantage of DeFi’s interconnected systems, enabling attackers to borrow massive amounts of collateral-free capital within a single transaction. The only condition? The loan must be repaid in the same transaction. This mechanism has been used to devastating effect. In April 2022, Beanstalk lost $182 million when an attacker used a flash loan to borrow over $1 billion, acquiring a two-thirds governance voting threshold. Without a governance timelock, the attacker passed a proposal to drain the treasury in one atomic transaction [5]. By 2025, flash loan attacks accounted for 37% of total protocol losses [10].
Oracle Manipulation
Oracles, which provide price feeds for liquidations and collateral valuations, are another weak spot. Attackers often exploit single-source price feeds or thin liquidity pools to manipulate prices artificially. This can lead to wrongful liquidations or allow undercollateralized borrowing. Over the last two years, oracle failures were behind 42% of critical DeFi protocol incidents [10], and audits reveal that nearly 100% of protocols using external price data have oracle manipulation vulnerabilities [7].
One notable example occurred in October 2022 when Mango Markets lost $114 million. The attacker used $10 million to inflate the MNGO token price on the protocol’s internal oracle, then borrowed against the inflated value to drain the platform [5]. In February 2026, Kelp DAO faced an even larger loss of $292 million when an attacker combined flash loans with oracle manipulation, exploiting a delayed price update and a single-source oracle aggregator [10].
"The most effective defense against flash loan-enabled oracle manipulation is implementing multi-source oracles with time-weighted average pricing (TWAP) or decentralized oracles that reduce reliance on any single price feed at a specific block." – Constantine Manko, Technical Lead, Soken [10]
Governance Token Risks
Governance token vulnerabilities target the democratic mechanisms that DeFi protocols use for upgrades and parameter adjustments. Attackers can use flash loans to temporarily acquire voting power, passing malicious proposals to drain treasuries or deploy harmful contract upgrades. The Beanstalk incident is a prime example, where the lack of a governance timelock allowed the attacker to execute a treasury-draining proposal immediately [5].
Key Vulnerabilities at a Glance
| Vulnerability | Severity | Prevalence in Audits | Primary Impact |
|---|---|---|---|
| Oracle Manipulation | High | ~100% | Wrongful liquidations, protocol draining |
| Reentrancy | High | ~30% | Fund drainage, state inconsistency |
| Flash Loan Exploits | High | Medium | Market manipulation, logic exploitation |
| Governance Token Risks | Medium-High | Low | Treasury theft, unauthorized changes |
The Rise of Multi-Vector Exploits
The interconnected nature of DeFi protocols means that exploiting one vulnerability can trigger cascading failures. Recent trends, particularly in 2025–2026, show a shift toward multi-vector exploits. These attacks combine smaller weaknesses across various systems – such as bridges, oracles, and governance mechanisms – to amplify their impact [11]. For institutional investors managing substantial capital in DeFi, thorough risk assessments have never been more critical.
Tools and Frameworks for Risk Assessment
Institutional investors need reliable tools to assess smart contract security, especially since current tools only catch 8–20% of exploitable bugs. Manual reviews remain crucial in bridging this gap[15]. These tools not only help quantify risks but also play a role in shaping strategies for addressing them.
CertiK Skynet for Protocol Scoring
CertiK Skynet offers a real-time security rating (0 to 100) based on six categories: Code Security, Fundamental Health, Operational Resilience, Governance Strength, Market Dynamics, and Community Trust[18]. For institutional investors, this provides a standardized way to evaluate protocols and track their security over time.
One key metric from Skynet is Audit Coverage, which calculates the percentage of a project’s source lines of code (SLOC) reviewed by professional auditors. The formula is: (Audited SLOC + Similar Code Components) / Total Project SLOC[18]. Skynet also measures Audit Freshness to ensure recent code changes are properly reviewed. Alarmingly, 90% of exploited projects in 2023 lacked audit coverage[15].
"Security ratings offer an objective way to monitor the security posture of Web3 projects, tracking whether it is improving or deteriorating over time." – CertiK[18]
Skynet goes beyond code analysis by examining governance centralization, focusing on privileged roles, admin controls, and token distribution. This helps identify governance risks, such as attackers using flash loans to manipulate voting power and disrupt treasury controls.
OpenZeppelin Defender for Monitoring
OpenZeppelin Defender complements CertiK by focusing on continuous operational monitoring. It enhances security through automated contract operations and real-time anomaly alerts. The platform’s Monitor module detects irregularities in contract behavior, flagging cybersecurity, financial, and governance risks[14][16]. Alerts can be configured for events like unusual oracle movements, large treasury outflows, or unexpected administrative actions.
The platform also includes an Access Control feature, which manages roles and permissions. This ensures upgradable contracts are protected by multisig wallets with enforced timelocks[16]. Notably, OpenZeppelin Defender is transitioning its tools to open-source versions ahead of a planned shutdown on July 1, 2026[14].
Additional Tools: Slither, Mythril, and Echidna
- Slither: This static analysis tool scans Solidity and Vyper code using 92 built-in vulnerability detectors and generates call graphs. It’s open-source and ideal for pre-audit screenings[15].
- Mythril: Using symbolic execution, Mythril analyzes EVM bytecode for multiple chains like Ethereum, Hedera, and Tron. Its enterprise version, MythX, offers advanced features. By examining various execution paths, it uncovers edge cases missed during standard testing[15].
- Echidna: A fuzzing framework that tests Solidity code by generating random inputs to break user-defined predicates. It’s especially useful for stateful fuzzing, where sequences of function calls ensure invariants like "total supply equals sum of all balances" remain intact under stress[13][15]. To ensure thorough testing, institutions should aim for at least 90% code coverage in their test suites[17].
| Tool Category | Primary Tools | Key Function | Cost |
|---|---|---|---|
| Static Analysis | Slither, Mythril, Securify2 | Scans code/bytecode for known vulnerability patterns | Free/Paid |
| Fuzzing | Echidna, Foundry | Generates random inputs to find edge cases | Free |
| Monitoring | OpenZeppelin Defender, Forta | Real-time anomaly detection and incident response | Paid |
| Mutation Testing | SuMo, Certora Gambit | Tests the quality of existing test suites | Free/Paid |
Risk Scoring Methods for Institutional Investors
Institutional investors need structured methods to evaluate DeFi protocols before committing capital. Unlike retail investors who might prioritize high APYs, institutions focus on objective metrics that translate complex security concerns into measurable criteria for building a portfolio.
Composite Risk Models
Composite risk models bring together eight key risk categories: smart contract, protocol, market, liquidity, counterparty, operational, regulatory, and systemic risks. Among these, Smart Contract risk is weighted the highest at 30%, followed by Protocol risk at 25% and Market risk at 20% [21]. Each category is scored on a scale of 1–5, where a score of 1 indicates protocols with multiple top-tier audits and no unresolved issues, while a score of 5 reflects unresolved vulnerabilities [23]. These scores are then weighted and used to guide decisions on position sizing and allocation limits. For example, blue-chip protocols might receive up to 40% allocation, while higher-risk protocols are capped at around 5% [22].
Tiered classification systems further refine these evaluations. For instance, Tier 1 protocols like Aave and Lido require a 25–50 basis point reduction in base yields to account for systemic risk and potential insurance costs. On the other hand, experimental protocols may need a deduction of over 200 basis points [22]. This approach incorporates additional metrics like TVL (Total Value Locked), audit history, and liquidity to further quantify risks.
TVL, Audit History, and Liquidity Metrics
Building on composite models, specific metrics provide deeper insights into risk. Total Value Locked (TVL) is often used as a measure of a protocol’s security maturity. For example, a protocol with over US$1 billion in TVL over an extended period indicates strong defenses and maturity. As of April 24, 2026, Lido’s TVL stood at US$21.67 billion, representing approximately 25% of the total DeFi market’s US$84.07 billion [22]. On the other hand, protocols with TVL under US$100 million or an estimated attack cost below US$10 million are considered high-risk [23].
Audit history is another critical factor. At least two independent audits from reputable firms conducted within the last six months are recommended [21][24]. It’s also important to distinguish between vulnerabilities that have been fully resolved and those that remain merely acknowledged.
Liquidity metrics complement TVL by assessing the overall market health. A Volume-to-TVL ratio above 0.3 is considered optimal to minimize slippage during exits. Additionally, liquidity pools should have TVL exceeding US$1 million to avoid significant price impacts. Longevity also matters – protocols operating for over 24 months are generally safer than newer ones [21][25].
| TVL Range | Score (TVL) | Longevity | Score (Longevity) |
|---|---|---|---|
| > US$480M | 1 (Lowest) | > 24 Months | 1 (Lowest) |
| US$120M – US$480M | 2 | 18 – 24 Months | 2 |
| US$40M – US$120M | 3 | 12 – 18 Months | 3 |
| US$10M – US$40M | 4 | 6 – 12 Months | 4 |
| < US$10M | 5 (Highest) | < 6 Months | 5 (Highest) |
Bestla VC‘s DeFi Yield Risk Framework

Bestla VC has developed a specialized risk assessment framework designed for institutional yield farming. This framework combines real-time security monitoring with multi-layered risk analysis, allowing for dynamic position management across various DeFi protocols. It integrates automated threat detection with manual governance reviews, addressing both technical vulnerabilities and potential economic attacks.
One key feature of the framework is its ability to calculate attack costs – whether through flash loans, governance manipulation, or oracle attacks – and use these figures to set allocation limits. Protocols with an attack cost above US$100 million are given higher allocation preferences, while those under US$10 million trigger automatic restrictions [23]. This methodology proved effective during the April 2026 Kelp DAO exploit, which caused a US$292 million loss and led to adjustments in insurance premiums for yield models [22].
The framework also incorporates real-time market data to continuously update risk scores. It monitors governance actions, ensuring protocols maintain 48–72 hour timelocks on code changes and enforce multisig controls with at least five signers. If a protocol’s security posture weakens, risk scores are automatically adjusted. This dynamic system has helped Bestla VC clients reduce security incidents by 67% and limit losses by 89% during the 2025 DeFi downturn [24].
Risk Mitigation Strategies for Institutional Yield Farmers
Once a risk scoring methodology is in place, institutions need actionable strategies to safeguard their investments. These measures are designed to proactively protect capital, especially in light of the DeFi sector’s troubling record – 44 security breaches leading to $482 million in losses during Q1 2026 alone[19]. It’s clear that mitigating risks is critical to preserving returns.
Multi-Audit Requirements and Timelocks
Strong defense starts with thorough audits and enforced timelocks. Institutions should only engage with protocols that have undergone multiple independent security reviews. A multi-layered audit approach includes automated formal verification, manual red-team assessments, economic threat modeling, and ongoing post-deployment monitoring[1][3]. This is crucial, as nearly 70% of exploit incidents in 2025 stemmed from vulnerabilities that proper audits could have flagged before deployment[26].
Take the Beanstalk attack as an example: the lack of a timelock allowed an attacker to exploit a vulnerability and siphon $182 million in a single flash loan-fueled transaction[5].
"A 48-72 hour delay gives the community time to detect and respond to potentially malicious changes" – Jorge Rodriguez, Risk Management at Lince Yields[5]
To avoid such scenarios, protocols should implement 48-72 hour timelocks on all high-impact functions – covering upgrades, parameter adjustments, and emergency kill switches. These should be paired with multisig wallets requiring 3-of-5 or 5-of-7 signer thresholds to eliminate single points of failure[26][1][3]. Institutions must also confirm that any vulnerabilities identified during audits have been addressed and re-audited, rather than simply relying on the presence of an audit badge[3]. This layered approach helps tackle risks early, improving overall security.
Automated Smart Contract Wallets
Automated smart contract wallets enable institutions to manage assets programmatically, with built-in safeguards to exit positions when risk thresholds are breached[4]. For instance, if a token peg deviates significantly or if total value locked (TVL) outflows exceed a specified limit within 24 hours, the system can automatically shift liquidity to safer options and unwind positions gradually[4].
These wallets integrate seamlessly with custody frameworks, enforcing governance rules, transaction policies, and multisig controls[20].
"Institutional participation requires strong custody, controls, and operational oversight" – BitGo[20]
For added security, institutions should favor non-upgradeable or non-admin-privileged contracts and work with MEV-aware builders to guard against front-running and other on-chain exploits[4]. Alerts for slashing events, validator downtime, or significant liquidity withdrawals can trigger automated defensive actions[4]. Keeping a portion of the portfolio in native ETH or stablecoins provides liquidity for emergencies like depegging or bridge failures[4]. Together, these measures create a safety net, reducing operational risks and improving risk scores.
Real-Time Exploit Detection and Exit Mechanisms
Advanced detection systems are key to identifying threats in real time. These tools monitor for unusual oracle price movements, sudden TVL spikes, or large, unexpected deposits and withdrawals – common precursors to exploits. Emergency pause or kill switches can then be triggered automatically or via multisig when specific risk thresholds are met[8][1].
"Security is no longer a one-time process – it is a continuous lifecycle" – Bloklab Oy[8]
Platforms like the Chainlink Runtime Environment enable automated responses to complex scenarios, such as shifting liquidity across chains or reinvesting rewards to limit exposure time[28]. Tools like Chainalysis Address Screening can check wallet addresses for links to illicit activity, ensuring institutions avoid high-risk counterparties[27].
Institutions should also implement multi-oracle aggregation by combining data from sources like Chainlink and Pyth, with fallback logic and sanity checks to mitigate flash loan risks[1]. Simulation tools like Tenderly or Foundry allow teams to test hypothetical flash loan attacks and evaluate outcomes before committing capital[1]. Additionally, setting position limits based on Expected Max Drawdown and stress-testing scenarios – such as a 50% token depeg or chain congestion – adds another layer of protection[1]. This comprehensive monitoring framework allows for quick responses to emerging threats, bolstering institutional defenses.
Best Practices for Bestla VC Clients
To build on the earlier discussion of risk mitigation strategies, these best practices are designed to help Bestla VC clients integrate security measures into their daily yield farming operations.
For institutional-scale operations, a disciplined approach that prioritizes security over flashy yields is essential. In 2026, the focus has shifted toward achieving risk-adjusted returns rather than chasing high advertised yields. Yield farming should be treated as a structured portfolio allocation exercise – more like managing investments than gambling on speculative opportunities [1].
A Tiered Capital Allocation Strategy
Divide your capital into three distinct tiers to balance stability and opportunity:
- Core (50–70%): Allocate this to regulated stablecoins and audited staking protocols. This forms the foundation of a secure portfolio.
- Satellite (20–40%): Invest in established automated market makers (AMMs) with strong track records.
- Opportunistic (0–10%): Reserve a small portion for newer, higher-risk protocols offering greater reward potential.
This approach ensures most assets remain in well-tested environments while allowing controlled exposure to emerging opportunities. To manage concentration risk, limit exposure within any single protocol to 3–10% of your total DeFi capital [2][30]. Back this strategy with thorough technical due diligence.
Due Diligence and Governance Security
Before committing capital, verify that protocols have undergone multiple independent audits, with vulnerabilities addressed and resolved [1][3]. For added governance security, ensure that critical protocol actions are protected by 48–72 hour timelocks and multisig wallets [1][29].
Operational Safeguards
On the operational side, take steps to protect against common threats:
- Use MEV-aware relays (e.g., Flashbots Protect) to prevent front-running and sandwich attacks during high-value transactions [3][29].
- Simulate strategies using mainnet forking tools like Foundry or Tenderly to stress-test scenarios such as oracle failures or token depegging [1][3].
- For leveraged positions, maintain collateral ratios well above the minimum – aim for 250% if the threshold is 150% – to withstand market volatility and avoid cascading liquidations [5].
- Keep part of your portfolio in native ETH or stablecoins to ensure liquidity during emergencies, particularly during network congestion [1][29].
"If you cannot identify exactly which risks you are taking on for a given yield, you are probably the exit liquidity." – Jorge Rodriguez, Risk Management at Lince Yields [5]
Real-Time Monitoring and Risk Management
Continuous monitoring is crucial for identifying risks as they arise. Use platforms like Forta or Tenderly for 24/7 monitoring of key metrics such as abnormal TVL spikes, large withdrawals, or oracle deviations [1][29]. Keep reserve capital for gas fees and verify rapid exit options through withdrawal windows.
To offset residual risks like smart contract vulnerabilities or token depegging, consider partial hedging with decentralized options or parametric insurance platforms such as Nexus Mutual [1][2]. Regularly revoke unnecessary ERC-20 approvals using tools like Revoke.cash, and secure all accounts holding more than $1,000 with hardware wallets [29].
Conclusion
Smart contract risk assessment today requires a multi-layered and continuous approach to security. The DeFi landscape in 2026 demands a blend of technical due diligence, real-time monitoring, economic threat modeling, and automated defense systems. This shift from chasing raw yield to prioritizing risk-adjusted returns signals a more mature market where long-term stability takes precedence over short-term speculation.
The lessons from past exploits are more critical than ever. Recent high-profile breaches highlight the devastating effects of smart contract vulnerabilities [5]. Because DeFi protocols are deeply interconnected, a single weakness in one can ripple across the system, jeopardizing entire portfolios. This interconnectedness makes revisiting historical incidents a key part of refining security strategies.
To manage these risks, effective strategies include diversifying capital allocation, implementing strong protocol safeguards, and maintaining continuous monitoring. At Bestla VC, we empower institutional clients with tools like automated portfolio analytics, cross-chain balance reconciliation, and real-time risk dashboards. Our DeFi Yield Risk Framework uses advanced techniques such as stress testing, Monte Carlo simulations, and programmatic controls to provide institutional-level security in decentralized environments. We also help clients establish exit triggers, verify governance measures, and adhere to the disciplined practices necessary for sustainable yield farming.
In DeFi, security is not a one-and-done task – it’s an ongoing process. By embedding continuous risk assessments into their operational strategies, institutional yield farmers can better navigate the challenges of the DeFi space while protecting their capital. This commitment to proactive risk management ensures resilience in an ever-evolving and complex ecosystem.
FAQs
How do I verify a protocol’s audits are complete and current?
To ensure a protocol’s audits are up-to-date, start by looking for publicly available reports from well-known auditing firms. Make sure these reports are recent and include clear timestamps. Firms like CertiK and OpenZeppelin are known for providing thorough and detailed audit findings.
You can also use tools like NomosLabs, which can help verify whether an audit has been completed and even provide security rankings. Always double-check the audit date against the protocol’s deployment date to confirm that the findings are still relevant.
What on-chain signals should trigger an immediate exit from a position?
On-chain signals that might call for an immediate exit include protocol vulnerabilities, exploit alerts, or unusual activity that could point to risks in smart contracts or liquidity. Keeping a close eye on these warning signs can help safeguard your investments and minimize potential losses in the DeFi space.
How should an institution size allocations based on smart contract risk?
Institutional investors looking to allocate funds to yield farming strategies need to approach the process with a clear understanding of the risks involved. Key considerations include smart contract vulnerabilities, oracle failures, and economic exploits. To manage risk effectively, higher-risk opportunities should be given smaller allocations, while protocols that are well-audited and demonstrate strong security measures can justify larger investments.
Diversification is another critical element. Spreading investments across multiple protocols and blockchain networks can help reduce overall exposure to potential failures or exploits. Additionally, maintaining a systematic approach – one that includes continuous monitoring and robust risk management practices – is essential for protecting capital while aiming for returns.


