Scaling institutional wallet transactions requires a clear focus on security, efficiency, and compliance. The crypto market operates 24/7, making it critical for institutions to manage high transaction volumes without interruptions or errors. Here’s a quick guide to the key steps:
- Strengthen Wallet Infrastructure: Use Multi-Party Computation (MPC) for secure, high-volume transactions. Ensure wallets are compatible with multiple blockchains and hosted across diverse environments (e.g., AWS, private clouds).
- Test Transaction Capacity: Simulate stress scenarios like rapid transaction bursts or offline modes to identify bottlenecks. Use fallback RPC endpoints to avoid delays.
- Define Governance Roles: Distribute wallet administration across multiple actors and implement tiered asset management (e.g., reserve vs. operating layers).
- Enhance Security: Leverage MPC and multi-signature wallets to eliminate single points of failure. Use hardware wallets and refresh key shares regularly.
- Automate Operations: Deploy event-driven triggers and policy engines to streamline approvals, enforce rules, and manage liquidity.
- Ensure Compliance: Implement eKYC, AML tools, and Travel Rule solutions. Align with regulatory standards like SOC 2 and EU DORA.
- Monitor and Scale: Use reliable SLAs, expand geographically, and integrate tools for real-time monitoring and reconciliation.
Evaluating Infrastructure Readiness
Assess Wallet Architecture
Before institutions scale up transaction volumes, they must ensure their wallet architecture can handle the increased demand. Secure Multi-Party Computation (MPC) has become a go-to solution for high-volume operations. It generates a single signature that works seamlessly across all blockchain protocols, eliminating the need for smart contracts. This simplifies the approval process and enables smooth cross-chain operations [8].
"Secure Multi-Party Computation (MPC) has emerged as the undisputed security technology of choice for digital asset custodians, exchanges, and institutions." – Blockdaemon [8]
Your wallet setup should support deployment in multiple environments – whether on-premises, private clouds, or public clouds like AWS. Hosting MPC nodes across various Cloud Service Providers enhances both resilience and availability [8]. For environments handling large volumes, secure computing enclaves like AWS Nitro can safeguard sensitive in-memory data during execution [9]. Avoid rigid N-of-N configurations, as losing a single key could result in complete fund loss. Instead, opt for flexible quorums such as 3-of-5, which ensure accessibility even during peak activity [8][11]. For wallets holding over $1 million, industry guidelines suggest using at least seven signers for added security [11].
Once your architecture is validated, the next step is to test how the system handles transactions under load.
Audit Transaction Handling Capacity
Before committing funds, run pilot tests to evaluate your system’s performance. Document every aspect of onboarding, backup processes, and signing workflows to uncover hidden bottlenecks [12]. Simulate real-world stress scenarios – such as revoked permissions, offline modes, outdated firmware, and rapid transaction bursts – to see how the system performs under pressure [12].
"A wallet that only works in a clean demo environment is not production-ready." – Daniel Mercer, Senior Crypto Security Editor [12]
To ensure reliable transaction broadcasting, set up fallback RPC endpoints and monitor their uptime and latency [5]. Relying on a single RPC provider increases risk, so use multiple services like Alchemy or Infura to avoid transaction delays during outages [5]. Check your wallet provider’s resource limits – such as API rate caps and sub-organization maximums – to confirm they align with your scaling needs [13]. Pay close attention to the Transaction Policy Engine, as overly complex rules (e.g., velocity limits or 2-of-N quorums) can become a bottleneck if poorly implemented [5][13].
Once transaction capacity is confirmed, focus on defining clear governance roles for smooth operations.
Define Governance and Operational Roles
For high-volume environments, clearly separating duties is critical. Blockdaemon recommends a three-actor model for the Institutional Vault to distribute risk effectively. Actor A manages Infrastructure and acts as the Policy Node 0 admin, while Actor B and Actor C oversee Policy Nodes 1 and 2, each operating from separate cloud accounts. This setup ensures sensitive in-memory data, protected by Nitro enclaves, cannot be accessed by a single entity [9].
Spread administrative responsibilities across different cloud accounts to enhance security [9]. Use a tiered approach to asset management: allocate 5-10% of assets to an "Operating Layer" for daily liquidity needs, while storing 90% or more in a "Reserve Layer" secured by air-gapped hardware or multi-sig vaults [14]. Software-based policy frameworks can automatically enforce approver quorums and conditional controls, reducing reliance on manual checks [8]. Mismanagement of private keys has already rendered nearly 20% of Bitcoin inaccessible [14], highlighting the importance of well-defined roles and responsibilities.
sbb-itb-c5fef17
How Institutions Secure Crypto: MPCVault’s Multi-Chain Wallet Explained
Implementing Security and Risk Controls
Scaling operations to handle billions in daily transactions demands more than just a solid infrastructure – it requires advanced security measures and risk management protocols. These controls ensure both safety and efficiency as operations grow.
Deploy Multi-Signature and MPC Solutions
To avoid single points of failure, institutions should leverage advanced cryptographic solutions like Multi-Party Computation (MPC). This method divides a private key into multiple shares, each stored on separate nodes. No single server or individual ever has access to the complete key [15][17]. For example, Blockdaemon uses MPC technology to safeguard over $2 billion in daily digital asset transactions [1]. The system typically includes three key components: signing nodes (holding key shares), a coordinator (managing the signing process), and a policy engine (enforcing rules like whitelists and rate limits) [15].
For multi-signature wallets, an M-of-N threshold ensures that a transaction only proceeds when a minimum number of signers (M) out of a total group (N) approve it [16][11]. For wallets managing over $1 million, use at least seven signers with a 50% signing threshold [11]. Avoid strict N-of-N configurations, as they can lead to issues if a key is lost. Instead, opt for flexible setups like 3-of-5 or 5-of-9 [11]. All signers should rely on dedicated, air-gapped hardware wallets for added protection [11][5].
"MPC ensures that no single individual, server, or institution is ever in possession of the complete key." – Vaultody [17]
Configure Granular Permission Systems
Efficient workflows can block unauthorized actions without sacrificing productivity. Use hierarchical approval systems, where routine tasks require fewer signatures, while high-value transactions demand full approval or senior management input [18]. Employ Role-Based Access Control (RBAC) to assign specific roles like "TreasuryOps", "Pauser", or "TradingBot", each with tailored permissions [18][11].
Introduce spending and velocity limits – daily, weekly, or monthly – to allow low-risk activities to proceed without full approval while capping potential losses [18][5]. Policy engines can analyze transaction details, enforcing rules based on asset types, destination addresses, or specific functions [18][5]. For critical changes, such as adding or replacing signers, require independent verification through methods like video calls combined with signed messages [11]. Adding timelocks between approval and execution provides an extra layer of security, offering time to catch errors or malicious actions before they take effect [18][11].
Diversify Custodians and Authorization Protocols
Spreading signing authority across various parties and environments strengthens defenses against insider threats, theft, and access loss. Assign signing roles to a mix of executives, developers, and operations staff, while also involving an external security partner [11]. To further reduce risks, store keys in different geographical locations and use diverse hardware wallet brands, such as Ledger and Trezor, to address manufacturer-specific vulnerabilities [11].
"The primary objective is to eliminate single points of failure and establish robust, distributed control over high-value assets and critical smart contract functions." – SEAL [11]
For MPC solutions, deploy signing nodes across multiple Cloud Service Providers to ensure uninterrupted transaction capabilities [8]. Rotate keys quarterly to limit potential damage from a breach, aligning with SOC 2 standards [5]. Use proactive secret sharing to refresh MPC key shares without altering the public wallet address, maintaining seamless operations [15].
Automate Transaction and Liquidity Management
Handling transactions manually doesn’t work when you’re dealing with massive volumes. This is where HD wallets (Hierarchical Deterministic wallets) come into play. These wallets can generate unlimited deposit addresses from a single seed, making it easier to manage thousands of user accounts and batch operations efficiently [13]. Pair these wallets with event-driven triggers – like webhooks or internal jobs – to automate tasks such as payouts, rebalancing, or user claims. Scheduled jobs can also handle recurring activities like yield compounding or periodic distributions, cutting down on manual intervention [13].
For liquidity management, set up systems to automatically transfer excess funds from hot wallets to cold storage once certain thresholds are reached. This maintains a balance between liquidity and security [4][7]. You can also implement programmatic policy engines to enforce rules like velocity limits, destination allowlists, and quorum-based approvals. Integrating API keys for system users streamlines signing and transaction requests [7][5][19]. For large-scale trading, execution algorithms like Time-Weighted Average Price (TWAP) and Volume-Weighted Average Price (VWAP) help minimize market impact and slippage [2].
To keep everything running smoothly, map all wallet, gateway, and exchange events into a unified ledger. This automates reconciliation, and setting predefined "normal ranges" ensures that any irregularities trigger immediate alerts [4].
Finally, consider stablecoin solutions to enhance settlement efficiency.
Integrate Stablecoin Solutions
Stablecoins have become a cornerstone for institutional settlements. By mid-2025, stablecoin markets hit new highs, with tokenized U.S. Treasuries surpassing $7 billion in value on public blockchains [7]. For high-frequency payouts, using Layer 2 networks like Polygon or Base can significantly reduce both costs and latency [22]. A great example is J.P. Morgan’s Kinexys platform, which processes over $2 billion in daily transactions using stablecoin-powered treasury tools [22].
Batch transfers allow you to send multiple transactions with a single approval, cutting down on operational overhead. Sponsored transfers – where a dedicated wallet covers network fees – remove the need for senders to hold native tokens. Programmable co-signers that auto-sign routine transfers via API further speed up high-frequency operations. Real-time webhook integrations can trigger backend processes immediately upon deposit confirmations, enabling instant vendor credits or secondary payouts [21].
"A stablecoin treasury cannot be ‘a wallet that holds funds.’ It must be an operating system with documented rules, enforceable permissions, and an auditable reconciliation process" [20].
- Alex, Stablecoin Insider
Capturing exact exchange rates and gas fees at the moment of payout and feeding this data directly into ERP systems automates reconciliation, removing manual bottlenecks [22].
But smooth settlements alone aren’t enough – you also need to ensure uninterrupted service.
Build High-Availability Infrastructure
For institutional operations, downtime simply isn’t an option. Multi-Party Computation (MPC) helps mitigate single points of failure by splitting key control across multiple devices and locations. Advanced schemes like FROST allow for high-throughput operations with two-round threshold signing [7].
Site-level redundancy is another must-have. Independent quorum paths ensure that operations can continue even if one facility experiences an outage [7]. Hosting wallets in confidential computing environments, such as AWS Nitro Enclaves or Azure AMD SEV, adds another layer of protection for sensitive data while enabling remote attestation [19]. Separating high-frequency money in motion (hot wallets) from "money in storage" (cold or reserve wallets) minimizes risk. Automated sweeps can shift funds based on liquidity needs [4].
Establish clear performance SLAs for metrics like peak transactions per second, approval latency, and uptime. Additionally, create crisis runbooks to handle scenarios such as quorum loss, vendor outages, chain forks, or key compromises. Real-time monitoring through immutable logs integrated with SIEM systems ensures you’re always prepared.
"Enterprise custody is security plus governance plus compliance. You need all three to scale" [7].
- Andrew Smith, Scalable Solutions
Ensuring Compliance and Regulatory Alignment
Implement eKYC and AML Measures
Regulatory compliance is non-negotiable when managing digital assets. In 2023 alone, global crypto AML fines hit $4.3 billion, with over 200 jurisdictions enacting FATF-aligned VASP AML laws [23]. The financial and reputational risks of non-compliance far outweigh the investment in proper measures.
Leverage automated eKYC systems featuring liveness detection and biometric matching to simplify customer onboarding. Use a tiered, risk-based approach: streamline processes for low-risk users while applying Enhanced Due Diligence to politically exposed persons (PEPs) and high-volume institutional clients [23][24]. For transaction monitoring, integrate blockchain analytics tools like Chainalysis, TRM Labs, or Elliptic into workflows. These tools can score wallet addresses and flag interactions with sanctioned entities in real-time [23][26].
"The biggest risk isn’t exposure to crypto – it’s not knowing you’re exposed at all."
- TRM Labs [26]
For transactions exceeding $1,000, automate Travel Rule compliance using platforms like Notabene, Sygna, or VerifyVASP to send originator and beneficiary information alongside transfers [23][24]. Configure systems to automatically flag transactions for Suspicious Activity Reports (SARs) at $5,000 or more and Currency Transaction Reports (CTRs) for amounts over $10,000 [28][29]. Real-time sanctions screening, using fuzzy logic to match against OFAC, EU, and UN lists, helps block prohibited transactions without disrupting legitimate ones [23].
While implementing eKYC and AML measures, ensure your wallet systems align with local data protection laws.
Verify Data Residency and Documentation
Data residency requirements differ across jurisdictions. For instance, the EU’s Digital Operational Resilience Act (DORA), effective January 2025, mandates strict ICT risk management and incident reporting standards. Non-compliance could result in penalties of up to 2% of global annual revenue or €10 million, whichever is higher [27]. Choose wallet architectures that meet these standards – edge wallets store keys locally, while cloud wallets may require region-specific hosting.
Ensure compliance by maintaining unique audit logs for every transaction, enabling instant reconciliation and tracking [6]. Use standardized frameworks like W3C Verifiable Credentials and Decentralized Identifiers (DIDs) for data portability and cryptographic verification during audits [30]. Regularly verify SOC 2 Type II and ISO 27001 certifications from custody and infrastructure providers [3]. Many jurisdictions also require retaining transaction and KYC data for at least five years [23][24].
With data compliance addressed, focus on robust risk management strategies to safeguard operations.
Develop Risk Management Protocols
To strengthen security, establish cross-functional teams dedicated to digital assets. These teams should coordinate strategy and enforce consistent risk controls [26]. Use geolocation blocking to prevent access from sanctioned regions like North Korea and Iran, and segregate client funds from operational funds to meet legal requirements [29][23][25].
Design operational systems to comply with the "tipping-off prohibition", which prevents notifying customers under AML investigation [23]. Address the "sunrise problem" by preparing for transactions involving VASPs in jurisdictions without Travel Rule requirements [23]. Maintain a compliance calendar that tracks annual AML audits, staff training sessions, and policy updates to ensure your program adapts to evolving regulations [23].
Monitoring and Expanding Wallet Capabilities
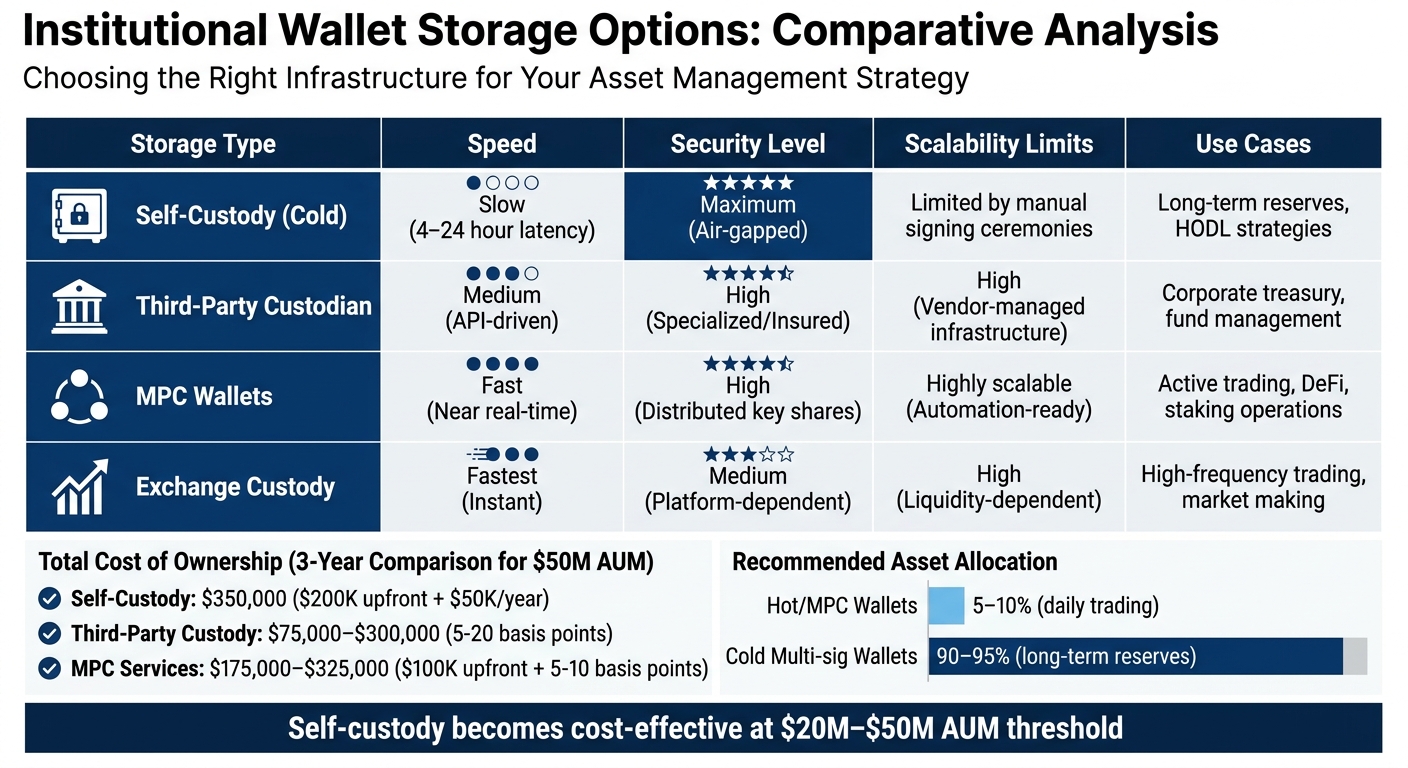
Institutional Wallet Storage Options: Security, Speed, and Scalability Comparison
These steps help refine your wallet infrastructure, ensuring it can handle growing transactional demands effectively.
Select Providers with Reliable SLAs
When choosing providers, focus on those with clear and dependable Service Level Agreements (SLAs). Look for transparent reporting, consistent API uptime, and fast response times. For example, cold storage solutions often come with SLAs ranging from 4 to 24 hours for signing processes and offline exports, which can create delays during high transaction periods [32]. Providers offering tools to monitor API uptime, system availability, and response times are preferable.
Set clear performance standards for your operations. Automated reconciliation and accounting reports can help avoid manual back-office bottlenecks as your business scales [7]. Leading custodians like Coinbase Prime and Anchorage Digital showcase their scalability through strong insurance coverage and impressive Assets Under Management (AUM) metrics [10].
"Treat custody as a control system, not a wallet. Define your risk model, choose the right operating and deployment model, demand audit evidence, and test recovery."
- Andrew Smith, Scalable Solutions [7]
Once you’ve secured reliable SLAs, expand your strategy to meet global operational needs.
Plan for Geographic and Ecosystem Scaling
With solid SLAs as a foundation, extend your infrastructure across regions to reduce local risks. Deploy vaults or Multi-Party Computation (MPC) nodes in key areas like North America, Europe, and Asia to ensure continuity during regulatory or technical disruptions [31][10].
Adopt custody solutions with policy engines designed to accommodate specific jurisdictional requirements, such as asset types, transaction limits, and approval workflows [7]. In regions with strict data residency laws, consider using dedicated Virtual Private Clouds (VPCs) or on-premises air-gapped systems to maintain control over cryptographic keys and logs [7][1]. Policy engines can also enforce geofencing, ensuring transactions are only initiated or approved from authorized locations [7]. Additionally, integrate real-time screening APIs for compliance with Know Your Transaction (KYT), Anti-Money Laundering (AML), and Travel Rule regulations during cross-border operations [7][31].
As you expand geographically, it’s also essential to evaluate your storage architecture for scalability.
Compare Storage Options for Scalability
A typical allocation strategy involves keeping 5–10% of assets in hot or MPC wallets for trading purposes, while the remaining 90–95% is stored in cold multi-sig wallets for long-term reserves [10]. Self-custody becomes more cost-effective than third-party custody when managing assets between $20 million and $50 million [10].
| Storage Type | Speed | Security Level | Scalability Limits | Use Cases |
|---|---|---|---|---|
| Self-Custody (Cold) | Slow (4–24 hour latency) | Maximum (Air-gapped) | Limited by manual signing ceremonies | Long-term reserves, HODL strategies |
| Third-Party Custodian | Medium (API-driven) | High (Specialized/Insured) | High (Vendor-managed infrastructure) | Corporate treasury, fund management |
| MPC Wallets | Fast (Near real-time) | High (Distributed key shares) | Highly scalable (Automation-ready) | Active trading, DeFi, staking operations |
| Exchange Custody | Fastest (Instant) | Medium (Platform-dependent) | High (Liquidity-dependent) | High-frequency trading, market making |
When considering the Total Cost of Ownership (TCO) over three years, self-custody typically requires an upfront investment of about $200,000 and $50,000 in annual costs, totaling $350,000. Third-party custody costs range from 5 to 20 basis points, translating to $75,000–$300,000 for $50 million in AUM. MPC services generally cost $100,000 upfront plus 5–10 basis points, totaling $175,000–$325,000 [10]. Ensure providers have SOC 2 Type II and ISO 27001 certifications, and routinely test recovery processes using tamper-evident media to maintain operational continuity [7][10].
Core Scaling Checklist
Scaling institutional wallet transactions requires building on strong infrastructure, security, and compliance foundations. Here’s a detailed checklist to guide the process.
Audit and Upgrade Infrastructure
Start by upgrading from basic single-signature setups to a hybrid custody model. This should combine MPC (multi-party computation) for warm wallets and HSM (hardware security modules) for cold storage [31][33]. With the digital asset custody market expected to grow from $683 billion in 2024 to over $1.35 trillion by 2029, this step is essential to remain competitive [33].
Leverage cloud-based key management services like AWS KMS or GCP Cloud HSM, or explore specialized Web3 providers to sign transactions securely in isolated enclaves [5]. Ensure redundancy by setting up fallback RPC endpoints and geographically distributed MPC nodes to prevent transaction delays caused by network issues [5][8].
To avoid signing malicious transactions, integrate transaction simulation APIs such as Tenderly, which preview the results before execution [5].
Implement Security Measures
Strengthen infrastructure with advanced security protocols. Use MPC for faster, blockchain-agnostic transaction signing while safeguarding key shares in HSMs or trusted execution environments (TEEs) [15][5]. MPC can achieve transaction signing speeds up to eight times faster than older cryptographic methods [33].
"MPC decentralizes the private key, so that no party ever has knowledge or possession of a complete key – mitigating the risk of insider misuse and theft by hackers."
- Blockdaemon [8]
Adopt a three-tier architecture to balance security and liquidity: Treasury (cold/strategic), Operations (warm/controlled), and Experiment (hot/disposable) [34][5]. Keep 5–10% of assets in hot or MPC wallets for daily transactions, while securing the majority (90% or more) in air-gapped hardware or multi-signature vaults for long-term storage [14].
Mitigate risks of key leakage by refreshing key shares regularly without changing the wallet’s public address [5]. Store recovery phrases using durable physical backups like metal plates to protect against fire, water, or corrosion [14]. Rotate key pairs every quarter and migrate funds as a precaution [5].
Integrate Compliance and Monitoring Tools
Adopt automated policy engines to enforce transaction rules, such as multi-signature requirements, velocity limits, and destination allow-lists, before execution [5][13]. Use real-time AML/KYT tools like Elliptic to monitor wallet activity and ensure compliance with the Travel Rule [7][35].
Integrate SIEM systems to maintain immutable audit trails [5][7]. Providers should comply with standards like SOC 2 Type II, ISO 27001, and EU DORA [7]. Implement the maker-checker principle, ensuring no single individual can initiate and approve high-risk actions. Maintain at least three administrators to handle privileged operations, ensuring continuity even if one admin loses access [35]. Export transaction data daily to internal ledgers for audit readiness and to catch any discrepancies [34].
Optimize for Performance and Ecosystem Expansion
Once compliance is in place, focus on performance and scalability. Use event-driven triggers with webhooks and background workers to convert external signals into automated signing requests, enabling high-volume operations [13]. Set up automated "halt switches" to pause transactions during events like stablecoin peg deviations (>0.5%) or bridge outages [34].
Incorporate stablecoins for liquidity management. By mid-2025, tokenized U.S. Treasuries had surpassed $7 billion in value on public chains, highlighting their growing adoption [7]. Deploy MPC nodes or vaults in strategic locations to reduce local risks and ensure operational continuity during technical or regulatory disruptions [31].
To guard against supply-chain risks, purchase hardware signing devices directly from manufacturers [14].
Establish SLAs and Incident Response Plans
Define robust Service Level Agreements (SLAs) with providers, specifying API uptime, system availability, and response times. Look for MPC solutions with signing latencies under 1 second, such as Fireblocks (800 ms) or Coinbase (under 1 second) [15]. Providers should also offer transparent reporting and automated reconciliation tools to streamline back-office operations as you scale [7].
Prepare for incidents with runbooks covering scenarios like stablecoin peg deviations or suspected key compromises [34]. Conduct monthly audits to revoke stale token approvals, reducing the risk of allowance abuse [34]. Additionally, institutional insurance policies for crypto holdings, often exceeding $250 million, can provide an extra layer of protection when paired with effective SLAs [31].
Conclusion
Scaling institutional wallet transactions has become a critical factor for staying ahead in the competitive landscape. By 2025, institutions and public companies are expected to hold around 4% of all mined bitcoin – approximately 852,000 BTC – and tokenized U.S. Treasuries have already surpassed $7 billion in value on public blockchains by mid-2025 [36][7]. With holdings of this magnitude, a structured approach to security becomes essential, as these assets are prime targets for sophisticated phishing attempts, social engineering tactics, and even physical breaches [8][36].
Success in this space hinges on balancing three essential pillars: security, governance, and compliance [7]. Andrew Smith from Scalable Solutions emphasizes this point:
"Enterprise custody is security plus governance plus compliance. You need all three to scale" [7].
Failing to adopt this holistic framework can lead to increased operational complexity, a larger attack surface, and fragmented controls – issues that regulators like those enforcing MiCA and DORA (effective January 17, 2025) will not tolerate [36][7]. An integrated approach strengthens every step of the process.
To implement these principles effectively, allocate resources toward skilled personnel, well-defined processes, and regular recovery testing [7]. Avoid single points of failure by leveraging Multi-Party Computation (MPC) or multi-signature setups – technologies that already secure over $2 billion in daily institutional digital asset transactions [1]. Policy engines can enforce precise rules, such as approver quorums, velocity limits, and destination allowlists, while robust logging and crisis response plans ensure readiness for unexpected events [7].
A well-designed infrastructure separates hot and cold custody, maintains a clean audit trail, and supports near real-time reconciliation [4]. Think of custody as a control system: define your risk model, choose operational strategies that fit your needs, demand regular audits, and rigorously test recovery procedures [7]. With regulatory standards tightening and institutional adoption growing, those who embrace these practices now will be well-equipped to scale confidently through 2026 and beyond, securing a competitive edge in the process.
FAQs
When should we switch from single-signature wallets to MPC or multi-sig?
Institutions should consider moving to MPC (Multi-Party Computation) wallets or multi-sig wallets when they need stronger security, better governance, and the ability to manage large-scale digital assets more effectively.
MPC wallets are particularly useful for reducing operational risks, safeguarding multi-chain treasuries, and protecting substantial digital holdings. They address critical security challenges, like private key compromises, by distributing key shares off-chain. This approach not only reduces risks but also helps institutions meet compliance requirements for managing high-value assets.
What stress tests best predict real production transaction bottlenecks?
When it comes to stress testing, the best results come from simulating conditions that closely resemble actual operations. For instance, running tests with 1,000 to 50,000 transactions and setting bandwidth limits at 30 MB/s can help pinpoint performance bottlenecks. Scenario-based tests are equally valuable – think of situations like sudden spikes in stablecoin withdrawals or disruptions caused by third-party failures. These methods offer practical insights, ensuring systems are ready to handle peak loads and uncover weak points before they become real problems.
How do we scale wallet automation without breaking AML and Travel Rule compliance?
To expand wallet automation while staying compliant with AML regulations and the Travel Rule, institutions should embed automated AML screening and transaction monitoring directly into their wallet systems. Implementing secure transaction signing workflows alongside hierarchical deterministic (HD) wallet structures allows for efficient and scalable transaction management while meeting compliance standards. This approach ensures tight control over key access, blocks unauthorized actions, and supports growth without sacrificing adherence to regulatory guidelines.


