Cross-layer APIs are transforming how blockchains communicate, solving the isolation problem that fragments liquidity, users, and smart contract states. These APIs provide a universal interface to connect different networks, simplifying data messaging and value transfers across chains.
Key takeaways:
- Problem: Blockchains operate in silos, creating inefficiencies like fragmented liquidity and delays in asset transfers (e.g., two-week lock-up periods for Layer 2 to Layer 1 transfers).
- Solution: Cross-layer APIs enable seamless communication across blockchains by abstracting technical differences (consensus mechanisms, data structures) and providing tools like omnichain tokens.
- Adoption: By 2025, cross-chain bridges locked $19.5 billion, with solutions like LayerZero supporting over 50 chains.
- Security: Protocol-level solutions (e.g., IBC) use on-chain verification for high security, while application-level solutions (e.g., Chainlink CCIP) rely on external networks for flexibility.
- Use Cases: Examples include staking ETH across Layer 2 networks and transferring assets faster without traditional delays.
These APIs are reshaping blockchain ecosystems by reducing fragmentation, improving efficiency, and supporting diverse applications.
Build a Cross-Chain dApp | Block Magic
Core Architectures and Protocols for Cross-Layer APIs
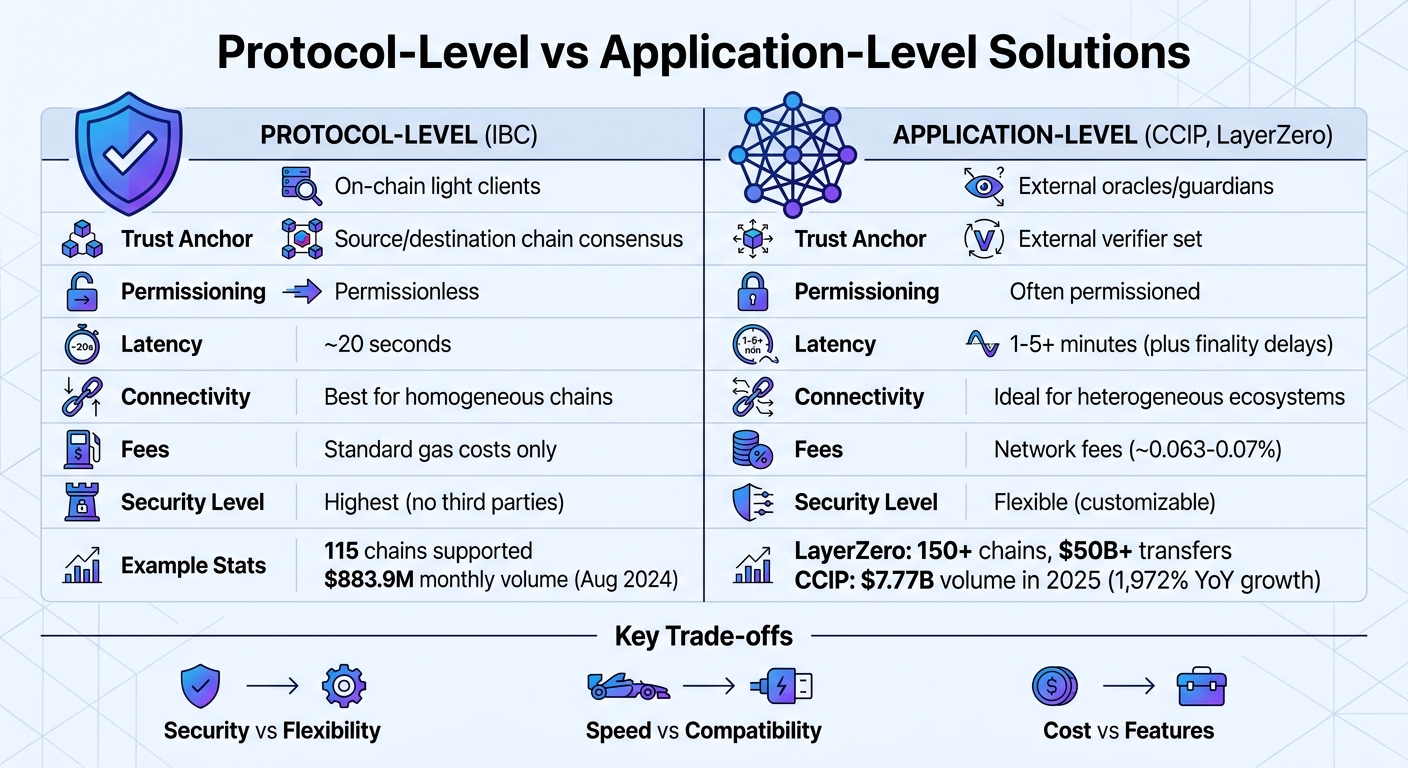
Protocol-Level vs Application-Level Cross-Layer APIs: Security, Cost, and Performance Comparison
Protocol-Level Solutions
Protocol-level solutions build verification directly into the blockchains they connect. Examples like IBC and Polkadot‘s XCM use on-chain light clients to verify block headers and state proofs[7][8]. This approach relies entirely on the consensus mechanisms of the source and destination chains, removing the need for trusted intermediaries.
IBC, for instance, currently supports 115 chains and handled $883.9 million in bridged volume in a single month as of August 2024[4]. The median packet latency is around 19–20 seconds[4][7], and it charges no additional fees beyond the standard gas costs on each chain. However, relayers can earn incentives through optional fee middleware.
"IBC’s light client-backed security is an improvement over systems that use a third-party verification bridge… because the chains themselves are performing the verification sans trusted third parties."
– Adi Ravi Raj, IBC Protocol Analyst, Interchain GmbH[4]
While highly secure, these solutions can be complex to implement and work best in ecosystems with similar consensus mechanisms. Expanding their use to connect EVM-based chains with non-EVM networks adds another layer of difficulty. This is where application-level solutions step in, offering a different approach to interoperability.
Application-Level Solutions
Application-level solutions shift verification responsibilities to external networks. Examples include Chainlink Cross-Chain Interoperability Protocol (CCIP), LayerZero, and Wormhole, which rely on decentralized networks of oracles, guardians, or verifiers to validate transactions[4][7][10].
Take Chainlink CCIP, for example – it processed $7.77 billion in volume in 2025, marking a 1,972% year-over-year increase[9]. It uses three independent oracle networks alongside a separate Risk Management Network to add an extra layer of security. LayerZero, on the other hand, connects over 150 blockchains and has facilitated transfers exceeding $50 billion[9]. Similarly, Wormhole’s Guardian network, made up of 19 validators, processes more than $300 million daily[9].
In October 2024, Lido introduced "Direct Staking" using CCIP’s Programmable Token Transfers. This allowed users on Arbitrum, Base, and Optimism to stake ETH and receive wstETH in one transaction, bypassing the typical 7-day bridging process between Layer 2 networks and Ethereum’s mainnet[11].
"With Chainlink CCIP’s Programmable Token Transfers, Lido’s Direct Staking simplifies staking across Layer 2 networks, improving liquidity for wstETH and enhancing cross-chain interoperability."
– Jakov Buratović, Master of DeFi, Lido[11]
While these protocols offer efficiency and flexibility, they come with distinct trade-offs that need to be considered carefully.
Comparing Security, Cost, and Decentralization
The choice between protocol-level and application-level solutions often comes down to trade-offs in security, cost, and decentralization.
| Feature | Protocol-Level (IBC) | Application-Level (CCIP, LayerZero) |
|---|---|---|
| Verification | On-chain light clients | External oracles/guardians |
| Trust Anchor | Source/destination chain consensus | External verifier set |
| Permissioning | Permissionless | Often permissioned |
| Latency | ~20 seconds | Typically 1–5+ minutes (plus finality delays) |
| Connectivity | Best for homogeneous chains | Ideal for heterogeneous ecosystems |
| Fees | Standard gas costs | Network fees (e.g., ~0.063–0.07%) |
Security remains a top concern in cross-layer API architectures. In 2025, cross-chain bridge hacks caused $2.8 billion in losses[9]. To address this, newer protocols are adopting modular security models. For example, LayerZero allows developers to customize their security setup by choosing specific combinations of verifiers, moving away from one-size-fits-all approaches.
Understanding these trade-offs is essential for selecting the right architecture when implementing cross-layer APIs in diverse blockchain environments.
Technical Requirements for Implementing Cross-Layer APIs
Infrastructure Requirements
Setting up cross-layer API integrations involves several critical components. At the core are endpoints, which are smart contracts deployed on each blockchain. These endpoints act as the main interface for sending, receiving, and verifying cross-chain messages [4]. Supporting these are Message Libraries (MessageLibs), which ensure the proper protocol logic is applied when composing, encoding, and verifying messages [4]. To maintain message authenticity, Decentralized Verifier Networks (DVNs) come into play. These networks use tools like ZK light clients, multisig committees, or native bridges to validate messages across chains. For instance, Deutsche Telekom MMS operates a DVN for LayerZero, ensuring robust verification processes through 2025 [5].
Other essential components include executors and relayers, which monitor verified messages, prepare transaction data, and handle gas fees on the destination chain [1][4]. Meanwhile, the transport layer – examples include IBC Core or LayerZero Endpoint – manages packet routing, delivery, and ordering [1][4]. High-availability RPC nodes and API gateways are also necessary for fetching state data and submitting transactions on both source and destination chains [2][5]. For monitoring and indexing, tools like Firehose or Substreams provide low-latency data tracking, while OpenTelemetry ensures smooth operation by monitoring JSON-RPC errors and latency [5].
These interconnected components create a robust framework for seamless cross-layer messaging, setting the stage for the skills and tools required during implementation.
Required Skills and Tools
To effectively implement cross-layer APIs, your development team must have strong command of blockchain-specific programming languages. For EVM-compatible chains like Ethereum, Arbitrum, and Optimism, Solidity is essential. Rust and the Anchor framework are key for Solana, while Move is used for Sui, IOTA, and Aptos. Developers should also be familiar with SDKs such as ethers.js, viem, and @eth-optimism/sdk for EVM chains; @solana/web3.js and Metaplex libraries for Solana; and cross-chain tools like @layerzerolabs/lz-definitions, @axelar-network/axelarjs-sdk, and @certusone/wormhole-sdk [2][6][13].
For development workflows, tools like the Create LZ OApp CLI can help quickly set up omnichain projects [13]. Local testing environments, including op-geth for Optimism, Arbitrum Nitro local nodes, and Axelar‘s Local Development suite, allow teams to simulate cross-chain message lifecycles before deployment [6]. Sensitive credentials like OFT_API_KEY, PRIVATE_KEY, and SOLANA_RPC_URL should always be stored securely in .env files to prevent accidental exposure [2]. Additionally, it’s crucial to use authentication modifiers like onlyFromCrossDomainAccount or validate sourceChain and sourceAddress in receiving contracts to safeguard against message forgery [6].
Equipped with the right skills and tools, developers can address the complexities of consensus and data structure differences.
Managing Consensus and Data Structure Differences
Cross-layer APIs simplify the challenges of varying consensus mechanisms and data formats by using standardized verification layers. These layers rely on DVNs or light clients to verify state transitions, eliminating the need for deep knowledge of each chain’s unique consensus model [1][4]. To account for differences in finality, developers can specify block confirmation counts or use tags like "finalized" and "safe" to ensure transactions are irreversible before executing cross-layer logic [5].
Data structure normalization is handled through standards such as Omnichain Fungible Tokens (OFT) or IBC packets, which provide unified data containers that abstract away chain-specific formats like EVM RLP or Solana’s base64-encoded transactions [2][13]. To avoid rounding errors, shared decimals should be managed separately from local decimals [2]. Considering the varying block times across chains, it’s important to use the counterparty’s timestamp or block height for timeout proofs on the source chain. Additionally, implementing retry mechanisms like retryPayload() on the destination chain can help recover from execution failures caused by gas price spikes or state changes, ensuring the messaging channel remains operational [6].
sbb-itb-c5fef17
Step-by-Step Guide to Integrating Cross-Layer APIs
Phase 1: Choosing the Right Architecture
Start by selecting the architecture that matches your project’s needs. For high-value assets like institutional stablecoins or tokenized securities, opt for high-security models such as ZK-proofs or light clients. For lower-risk scenarios like gaming tokens or social interactions, faster committee-based multisig models may be a better fit [1].
Next, decide between coupled and separated architectures. Coupled systems combine the interface, verification, and execution into one package, making them easier to manage but tying you to a single vendor’s security model. Separated architectures, on the other hand, allow flexibility by decoupling these layers. This means you can, for instance, upgrade from multisig to ZK-proofs without rewriting your application code [12].
Your asset handling approach is another key factor. Options include:
- Lock-and-Mint: Creates wrapped tokens.
- Burn-and-Mint: Maintains canonical tokens across chains.
- Liquidity Pools: Facilitates atomic swaps [1].
Choose based on whether you need synthetic representations or native asset movement. Additionally, ensure your architecture supports the specific L1 and L2 networks you’re targeting. Some protocols offer "Universal APIs" that work seamlessly across both EVM and non-EVM chains, such as Solana [2].
After finalizing your architecture and asset handling method, you can move on to configuring and validating your API setup.
Phase 2: Configuring and Validating APIs
Once you’ve chosen your architecture, it’s time to set up and validate your APIs for smooth cross-chain interactions.
Start by requesting transaction quotes to identify available routes. Execute the transaction steps and poll the status endpoint until the process is complete [14][17]. For example, LayerZero’s Value Transfer API supports over 450 tokens across 150+ blockchains, all through a single integration point [14]. Use standardized chain names from libraries like @layerzerolabs/lz-definitions to avoid typos and ensure accuracy [2].
Enable pre-validation by setting the validate parameter to true before generating transaction calldata. This step checks wallet balances and contract parameters upfront, reducing the risk of failed transactions [2]. Use EIP-55 checksums for blockchain addresses and automate token approvals by verifying current allowances with allowance() before submitting transactions [2][17].
For read operations, rely on safe or finalized block identifiers to avoid inconsistencies caused by chain reorganizations [5]. When using WebSocket subscriptions, implement circuit breakers to handle dropped connections and ensure idempotent re-subscription [5]. If you’re working with Solana, include setComputeUnitLimit and setComputeUnitPrice instructions to keep transactions competitive without over-allocating resources [5].
Phase 3: Testing and Deployment
Before deploying, thoroughly test your integration using local simulators. Tools like Chainlink’s CCIP Local Simulator can significantly speed up development cycles, reducing them from minutes to seconds [5][3]. For bridges that don’t emit destination events, use derived data requests to monitor specific transaction hashes in source-side logs [18].
When transitioning to mainnet, use canary budget caps to limit minting and unlocking rates. This approach ensures stability during the initial phase. For instance, Lido successfully migrated wstETH to Chainlink’s CCIP Cross-Chain Token (CCT) infrastructure in 2026, using operational guardrails like Token Developer Attestation to manage risks [3]. Similarly, Worldcoin adopted CCT for secure token transfers between World Chain and Ethereum, implementing rate limits and developer attestations [3].
Set up unified monitoring with OpenTelemetry, tagging spans with rpc.method and rpc.jsonrpc.error_code to track error budgets [5]. For enhanced reliability, consider hedged reads: send identical requests to two providers with a slight delay and accept the first "finalized" result [5]. Finally, implement on-chain kill-switches and maintain detailed runbooks for emergencies. This is particularly critical given that bridge hacks have caused approximately $2.87 billion in losses since 2016, representing nearly one-third of all blockchain-related exploits [16].
Security, Settlement, and Operations Management
Ensuring Security and Reliability
When choosing a verification model, it’s important to balance security, cost, and latency. Light clients and ZK-proofs provide the strongest security guarantees, but they come with higher costs and slower performance. On the other hand, committee-based multisig systems are faster and cheaper but rely on trust in a known validator group. Optimistic verification strikes a middle ground by using fraud proofs with challenge windows, such as the 7-day delay for L2-to-L1 messages on Optimistic Rollups, which offers a mix of security and capital efficiency [1][6].
To enhance security, consider layered defenses. For example:
- Misbehavior detection: Freeze faulty connections to prevent potential issues.
- Rate limits: Restrict rapid value exits to avoid exploitation.
- Circuit breakers: Temporarily disable risky message types when needed [4].
For replay protection, employ unique incrementing nonces, track executed message hashes on the destination chain, and include the origin ChainID in each message hash [6]. It’s also wise to decouple your interface from the verification system, allowing you to switch security modules – like moving from multisig to ZK-proofs – without needing to rewrite the code [12]. If the destination chain lacks logs, calculate expected transaction hashes through derived data requests to ensure all cross-chain activity is captured [18].
Monitoring Transaction Settlement
Once security measures are in place, tracking the progress of cross-layer messages becomes critical. To do this, monitor eight key timestamps for every cross-layer message:
- Submission (t0)
- Source inclusion (t1)
- Source finality (t2)
- Proof readiness (t3)
- Relay posting (t4)
- Destination inclusion (t5)
- Destination finality (t6)
- Spendability (t7) [19]
Keep an eye on latency metrics like p50, p95, and p99 for both "time-to-spend" (what users experience) and "finality-to-finality" (your risk exposure). These metrics help identify performance outliers [19].
"Bridge latency isn’t just one simple number; it’s made up of several components, including source finality, proof generation, and relayer cadence." – AUJay, Head of Platform, 7BlockLabs [19]
For reliable settlement confirmation, use the RPC "finalized" tag instead of relying on block-depth heuristics [19]. To avoid monitoring gaps during outages, use at least two RPC providers per chain and reconcile data between them [19]. For context, IBC’s median latency is approximately 19 seconds, while LayerZero ranges from 107 seconds (Arbitrum to Base) to 298 seconds (Arbitrum to Ethereum Mainnet) [4].
Evaluating Costs and Benefits
Operational costs are another critical factor, impacting both source and destination chains. L1 transactions, such as those for submitting proofs or state data, are typically the most expensive [6]. Following the EIP-4844 upgrade, Layer 2 data availability costs fell by over 90%, leading to a doubling of cross-chain transaction activity within 150 days [3].
| Protocol | Avg. Message Cost (Mainnet) | In-Protocol Fees |
|---|---|---|
| Hyperlane | $1–$5 | None |
| LayerZero | $2–$10 | None (users pay DVNs/Executors) |
| Wormhole | $3–$8 | Via Relayer Network |
| Axelar | $5–$15 | Requires destination gas |
| IBC | Transaction costs only | None (public infrastructure) |
To minimize costs, batch multiple user operations into a single L1 proof and reduce the data footprint by using tightly packed bytes or uint arrays instead of verbose structs [6]. A policy engine can also help by selecting the most efficient routes based on security, cost, and liveness, with a preference for native paths [3]. Regularly monitor metrics like "cost per successful message" and "P95 finality" to evaluate financial and operational efficiency [3].
Conclusion: The Future of Cross-Layer APIs in Blockchain
Cross-layer APIs are shaping the blockchain ecosystem into a more unified and efficient network. The move from traditional "lock-and-mint" bridges to an intents-based architecture has already shown impressive results. Take Across Protocol, for instance – it has facilitated over $35 billion in cross-chain volume and 15 million transactions without a single exploit. This success stems from its innovative model, where professional relayers use their own capital to fulfill user orders, eliminating the need for user-funded liquidity pools.
"The architecture removes the honeypot. There’s no user-funded pool to drain." – Across Protocol [20]
Emerging standards like ERC-7683 (Crosschain Intents) and ERC-7802 (SuperchainERC20) are also driving progress. These frameworks simplify asset transfers between chains through burn/mint processes, reducing liquidity fragmentation and allowing developers to interact with a single interface instead of juggling multiple protocols [15]. These improvements are not just theoretical – they’ve already boosted cross-chain activity and streamlined interoperability.
The next frontier involves abstracting complexity even further. By coordinating transactions across bridges and DEX aggregators, these APIs optimize liquidity and pricing for users [15]. Security is advancing too, with decentralized verifier networks (DVNs) offering customizable security solutions through quorum-based ZK-proofs and committee attestations [3].
Cross-layer APIs are also enabling autonomous AI agents to handle tasks like bridging tokens, fetching live quotes, and executing cross-chain swaps without human input [20]. With intents-based bridging now delivering transaction completions in about 2 seconds [20], the infrastructure is ready to support the next wave of decentralized applications. These developments equip developers with tools to build scalable, secure blockchain solutions that prioritize both performance and safety.
FAQs
How do cross-layer APIs differ from traditional bridges?
Cross-layer APIs take a different approach to interoperability compared to traditional bridges. Traditional bridges tend to bundle interface, verification, and execution into rigid, inflexible systems. In contrast, cross-layer APIs – such as the MetaLayer API – simplify this complexity. They provide a unified interface that seamlessly connects multiple liquidity sources and exchange paths. This approach cuts down on operational overhead, boosts efficiency, and gives developers access to optimized routes without the hassle of juggling multiple protocols.
Which verification model is safest for my app?
The best verification model for your app hinges on its specific security requirements, tolerance for latency, and trust assumptions. On-chain verification, which includes methods like light clients or zero-knowledge (zk) proofs, ensures a high level of security by validating events directly on the blockchain. However, this approach can come with increased latency. On the other hand, external verification layers, such as zk proofs or multisig setups, deliver quicker finality. The trade-off? They depend on third-party trust or cryptographic proofs, which can introduce added complexity.
What do I need to integrate a cross-layer API?
To set up a cross-layer API, start by creating standardized, machine-readable contracts. Examples include AsyncAPI for WebSocket and OpenRPC for JSON-RPC. These contracts ensure clear communication protocols between systems. Next, implement secure cross-chain primitives like messaging protocols and pessimistic proofs to maintain reliability across networks.
Make sure your development environment is compatible with blockchain SDKs and APIs. For instance, tools like LayerZero can simplify cross-chain transfers and messaging. Following these steps ensures smooth interaction between Layer 1 and Layer 2 blockchains.


